Specialists from the Dutch information security company SanSec have discovered that the hacker group Lazarus (aka Hidden cobra) practices web-skimming and hacks online stores. They also managed to find connection between North Korean hackers and MageCart attacks.
Let me remind you that initially the name MageCart was assigned to one hack group, which was the first to introduce web skimmers (malicious codes) on the pages of online stores to steal bank card data.But this approach turned out to be so successful that the group soon had numerous imitators, and the name MageCart became a common name, and now it unites a whole class of such attacks. If in 2018 RiskIQ researchers identified 12 such groups, then by the end of 2019, according to IBM, there were already about 40 of them.
Let me remind you that hackers even managed to inbuild a Magecart script to collect bulling information on Forbes subscription website.
“During such attacks, hackers usually gain access to the server of the online store, any related resources or third-party widgets, and are able to download and run malicious code”, – say SanSec researchers.
Typically, a web skimmer is downloaded only on the checkout page and automatically steals the payment card data when the user enters them at checkout. This data is sent to a remote server, controlled by cybercriminals, and hackers collect it, use it themselves or sell it on the darknet.
Mass attacks on online stores have been ongoing approximately since mid-2018. Among the most significant victims of recent attacks are Wongs Jewelers, Focus Camera, Paper Source, Jit Truck Parts, CBD Armor, Microbattery, Realchems and Claire’s.
A recent SanSec report connects specific domains and IP addresses used for recent MageCart attacks on US stores with the previously known hacker infrastructure of “government” hackers. So, SanSec founder Willem de Groot writes that the gathered evidence indicates that the famous North Korean hack group Lazarus may stand behind a series of attacks on American stores.
“How Hidden cobra gained access (to compromised stores) is still unknown, but attackers often use phishing attacks (malicious emails) to retrieve passwords of employees from the retail industry”, — write the expert.
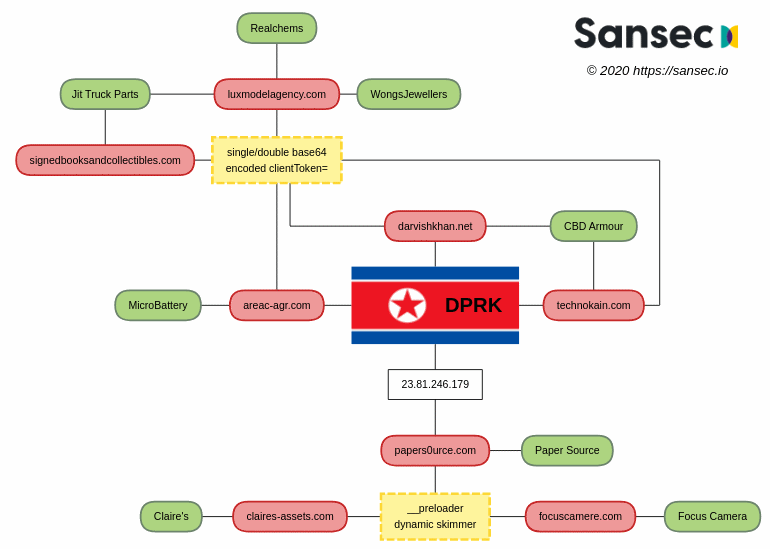
Green is a hacked store. Red – Lazarus-controlled data extraction nodes. Yellow – unique techniques linking attacks and malicious code.
I also remind you that hackers hide MageCart web skimmers in image metadata and even managed to hide malicious code behind favicon.