Speaking at the Virus Bulletin 2020 conference, ESET specialists spoke about the discovery of a new government cybercriminal group XDSpy, which has been active since at least 2011. At the same time, the researchers did not specify which government the hackers work for.
Over the past years, the group has quietly attacked state and private companies in Belarus, Moldova, Russia, Serbia and Ukraine. The list of countries may be incomplete, as many hacker campaigns wait to be discovered. The group focuses on exploration and theft of documents.“Currently, XDSpy activity has stopped, and this happened after the warning published by the Belarusian CERT in February this year. In fact, then the experts discovered one of the malicious hacker campaigns, which was described in detail in the document. Information from the Belarusian CERT became the starting point for launching the ESET investigation and helped analysts discover past XDSpy operations”, – told ESET researchers.
The main tool of the hack group was a set of malware called XDDown. Although the malware, according to the researchers, was not the most modern, it was enough to infect the machines of victims and collect sensitive data. In essence, XDDown is a downloader used to infect and then download various plug-ins that perform specialized tasks.
Actually, due to this feature security solutions did not detect XDDown.
Among the XDDown modules were found:
- XDREcon: a module for scanning an infected host, collecting technical data and information about the OS, and sending information to the command and control server;
- XDList: a module for searching files with certain extensions (Office files, PDF files and address books) on the infected machine;
- XDMonitor: a module that monitors which devices were connected to the infected host;
- XDUpload: a module that uploads the necessary files to the XDXpy control server;
- XDLoc: a module for collecting information about nearby Wi-Fi networks, which was used to track the movement of victims using public maps;
- XDPass: module that extracts passwords from local browsers.
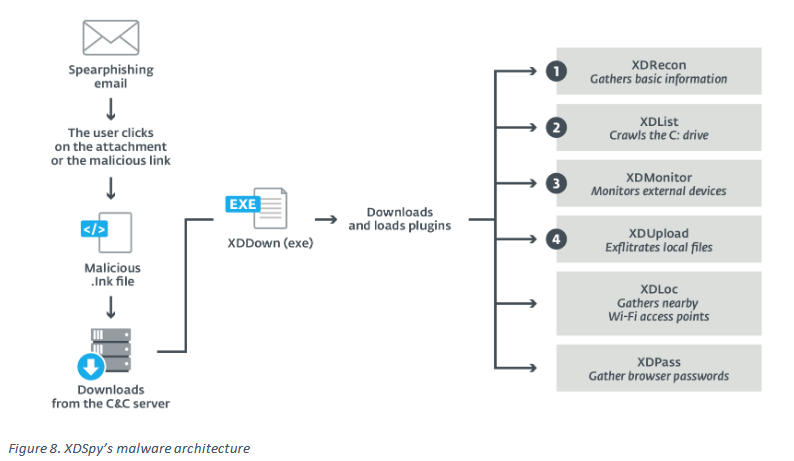
The XDSpy malware was distributed by mail using targeted phishing attacks. So, it is known that the group used decoy letters related to lost and found items, as well as the coronavirus pandemic. These emails contained malicious attachments, including Powerpoint files, JavaScript, ZIP or shortcuts (LNK). Downloading and running any of these files resulted in infection.
According to experts, a number of factors point to the fact that XDSpy is a government hack group. For example, malicious modules intentionally lack a resilience mechanism, that is, XDDown had to reload each module after rebooting the infected machine.
In addition, some XDDown plugins were equipped with special “switches” that removed them after a certain date. All of this suggests that XDSpy relies on secrecy, tries to remain unnoticed and avoid disclosing its tools. This is typical mode of work of governmental hackers.
“Thus, they used the same code base for 9 years, and also had the ability to bypass some security products through obfuscation”, — summarize the experts.
Indicators of compromise have already been published on GitHub, including all known details about the XDSpy framework and their malware.
Let me remind you that Lookout experts also discovered link between Chinese hackers and defense contractor. We also highly recommend to read the epic story from Crowdstrike about the creation of the Chinese Comac C919 aircraft, which was accompanied by hacker attacks and cyber espionage.