The US Department of Justice has charged six Russian citizens that supposedly were the members of the Sandworm group (aka Telebots, BlackEnergy, Voodoo Bear, and so on), one of the most prominent state-sponsored hacker groups. The group is accused of attacks by NotPetya, KillDisk and OlympicDestroyer.
The American authorities claim that all of the defendants serve in Unit 74455 of the Main Intelligence Directorate of Russia (Unit 74455) and, on the orders of the Russian government, have carried out cyberattacks with the aim of destabilizing other countries, interfering in their internal politics, causing damage and monetary losses.Specifically, the DOJ links the Sandworm group to the following known incidents:
- Attacks on the government and critical infrastructure of Ukraine: from December 2015 to December 2016, attacks were carried out on the power system of Ukraine, the Ministry of Finance and the State Treasury Service using BlackEnergy, Industroyer and KillDisk malware;
- French elections: in April-May 2017, prior to the French elections, were recorded targeted phishing attacks and related hacking attempts, targeting the political party La République En Marche! French President Macron, other French politicians and local authorities in the country;
- Business and critical infrastructure worldwide (NotPetya): On June 27, 2017, massive NotPetya attacks began, affecting computers around the world, including Heritage healthcare facilities in Pennsylvania, a subsidiary of FedEx Corporation, TNT Express BV, and a major pharmaceutical manufacturer in the United States, which ultimately incurred losses of $1 billion;
- Organizers, participants, partners and visitors of the Winter Olympics in Pyongyang: from December 2017 to February 2018, phishing campaigns and malicious mobile apps attacked South Korean citizens and officials, Olympic athletes, partners and visitors to the Olympic Games, and officials from the International Olympic Committee;
- IT systems of the Pyongyang Winter Olympics (Olympic Destroyer): From December 2017 to February 2018, were recorded attacks on systems serving the Pyongyang Winter Olympics. It culminated in a devastating attack on the opening ceremony of the Olympic Games on February 9, 2018, using the Olympic Destroyer malware;
- Investigations into Novichok poisoning: In April 2018, targeted phishing campaigns aimed investigations of the Organization for the Prohibition of Chemical Weapons (OPCW) and the United Kingdom’s Defense Science and Technology Laboratory (DSTL) on the poisoning of Sergei Skripal, his daughters and several British citizens with nerve agent;
- Attack on Georgian government institutions: in 2018, a spear-phishing campaign targeting a large media company was noticed, an attempt was made to compromise the parliament’s network in 2019, and in 2019 large-scale deface attacks were noticed on a variety of websites.
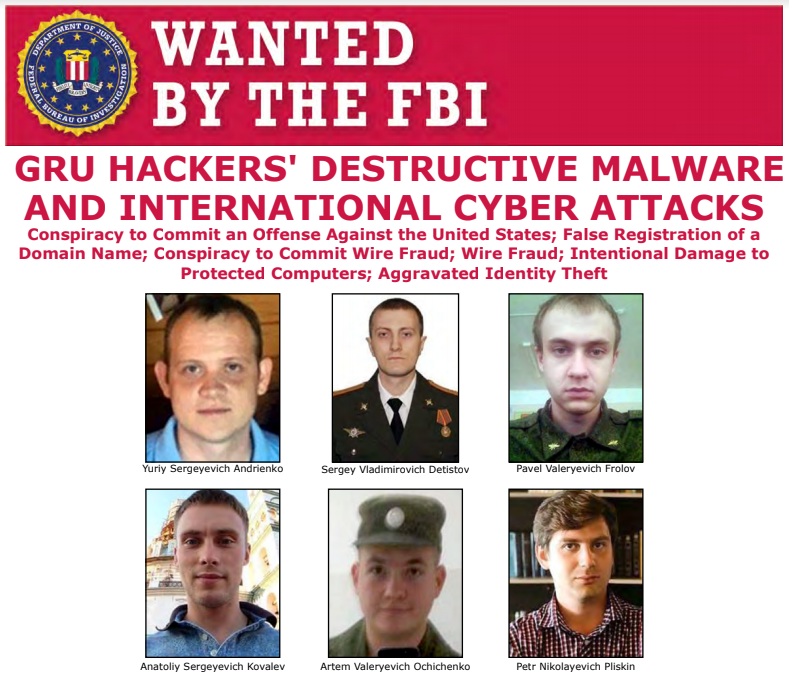
According to court documents, the six GRU officers charged are responsible for the following crimes:
| Defendant | Prosecutions |
| Yuriy Sergeevich Andrienko | Development of NotPetya and Olympic Destroyer malware components. |
| Sergey Vladimirovich Detistov | Development of NotPetya malware components, as well as preparation of phishing campaigns aimed at the Winter Olympic Games in Pyongyang. |
| Pavel Valerievich Frolov> | Development of the KillDisk and NotPetya malware components. |
| Anatoliy Sergeevich Kovale>v | Designing phishing campaigns targeting: members of La République En Marche !; DSTL employees; IOC members and Olympic athletes; employees of the Georgian media. |
| Artem Valerievich Ochichenko | Participation in phishing campaigns against partners of the Winter Olympic Games in Pyongyang in 2018; Technical intelligence in relation to the official domain of the Parliament of Georgia and an attempt to gain unauthorized access to its network. |
| Petr Nikolaevich Pliskin | Development of NotPetya and Olympic Destroyer malware components. |
At a press conference, US officials said that the group’s attacks were often based on the chaotic use of destructive malware, which not only led to financial losses among thousands of companies, but also put human lives at risk, demonstrating disregard for any rules and regulations.
“This case demonstrates that no country in the world has used its cyber potential as maliciously and irresponsibly as Russia, which has purposelessly inflicted unprecedented collateral damage in order to achieve small tactical advantages and satisfy its attacks of aggression”, — said Assistant Attorney General for National Security John Demers.
John Demers also spoke about the attack on the infrastructure of the Olympic Games, which occurred after the Russian athletes were banned from participating in the Olympics due to doping, as well as the NotPetya ransomware, which was originally aimed at Ukraine, but the group lost control, causing damage to companies all over the world.
All six accused are currently at large in Russia. If they are detained and brought to an American court, each of them faces a sentence of several decades in prison.
Let me remind you that we recently talked about the fact that the FBI and NSA discovered Drovorub malware, created by Russian Intelligence services. And that Russian hackers attacked hosting sites in Georgia.





