BlueKeep Attack Warnings Didn’t Affect Users
Researchers from the SANS Institute (USA) over the past few months have been monitoring the situation with the use of patches that fix the BlueKeep vulnerability in Windows, and with the use fof Shodan recorded the number of vulnerable computers connected to the Network. Experts concluded that the massive warnings about BlueKeep attacks did not affect the desire of users to apply patches.
Recall that over the past week there have been reports of signs of exploitation of BlueKeep in real attacks. Attackers tried to infect computers with cryptocurrency mining malware. As a result, Microsoft once again called on users to install patches that eliminate the vulnerability, which the company released back in May of this year.“After a news of “mass exploitation” of a specific vulnerability hits mainstream media, even organizations that don’t have a formal (or any) patch management process in place usually start to smell the ashes and try to quickly apply the relevant patches. Since media coverage of the recent BlueKeep campaign was quite extensive, I wondered whether the number of vulnerable machines would start diminishing significantly as a result”, — writes Jan Kopriva, SANS researcher.
Nevertheless, as it turned out, administrators are in no hurry to follow the company’s recommendations. According to the researchers, since May the level of “patched” systems has been steadily declining.
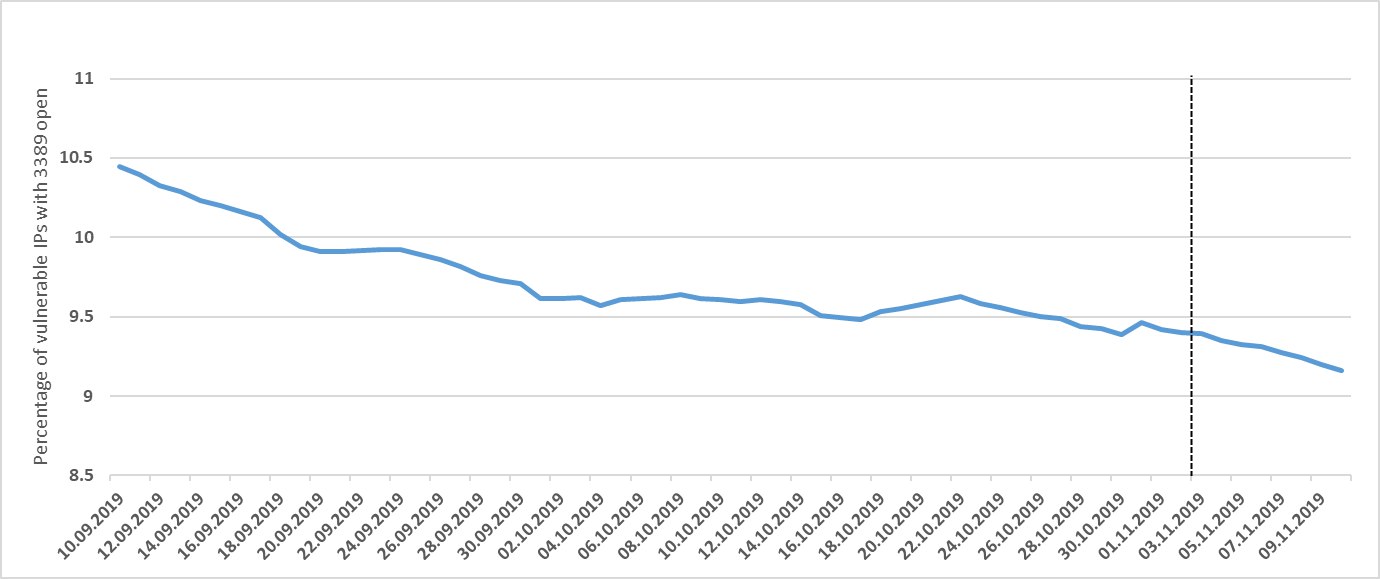
“As we may see, the percentage of vulnerable systems seems to be falling more or less steadily for the last couple of months and it appears that media coverage of the recent campaign didn’t do much to help it”, — noted researchers.
Nevertheless, the threat of BlueKeep is still relevant, the researchers emphasize. Despite the decline in the number of unpatched machines, there are a fairly large number of vulnerable systems that can become an attractive target for attackers.
Read also: Facebook reports another data leak
Researchers note that even given the presence of hundreds of thousands of vulnerable systems, we can only hope that the worm that everyone is waiting for will not appear in the near future.



