In May 2020, Trend Micro Zero Day Initiative researchers reported about five unpatched 0-day vulnerabilities in Windows, four of which were at high risk.
The three vulnerabilities identified as CVE-2020-0916, CVE-2020-0986, and CVE-2020-0915 scored 7 out of 10 on the CVSS vulnerability rating scale.In fact, these three problems allowed an attacker to elevate their privileges on a vulnerable system to the current user level. However, attackers who decide to exploit these bugs would first have to gain low-privileged access to the target system.
The root of these problems lies in the splwow64.exe host process running in user-mode: user-supplied input was not properly validated before the pointer was dereferenced.
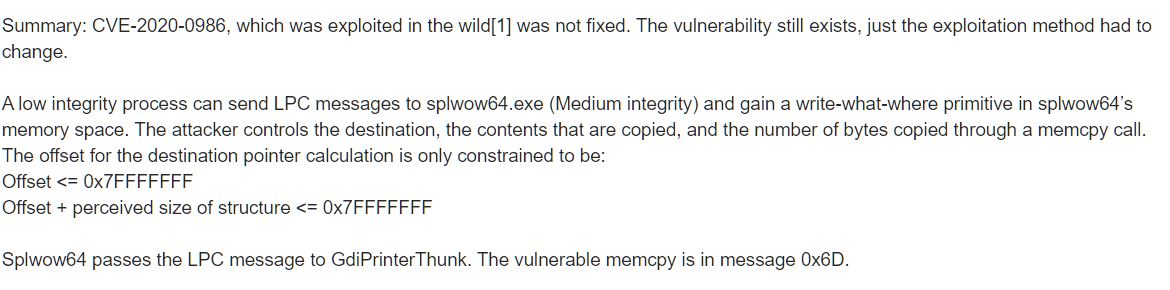
Now, six months later, Google Project Zero specialist Maddie Stone discovered that Microsoft’s June patch did not fully fix the CVE-2020-0986 vulnerability, and it can still be exploited by elevating privileges to the kernel level.
“In May, @oct0xor discovered CVE-2020-0986 in Windows splwow64 was exploited itw as a 0day. Microsoft released a patch in June, but that patch didnt fix the vuln. After reporting that bad fix in Sept under a 90day deadline, it’s still not fixed. The original issue was an arbitrary pointer dereference which allowed the attacker to control the src and dest pointers to a memcpy. The “fix” simply changed the pointers to offsets, which still allows control of the args to the memcpy”, — wrote to Maddie Stone on her Twitter.
In a brief technical report on the new issue, identified as CVE-2020-17008, Stone explains the mechanics of the old-new vulnerability, and also includes a simple PoC exploit in the report.
Microsoft engineers were notified of this error back on September 24, 2020 and planned to release the patch as part of November “update Tuesday”, however, some problems were discovered during the patch testing phase, so the patch was postponed to January 2021.
As you know, Google Project Zero specialists adhere to strict rules and always give companies and developers 90 days to fix vulnerabilities.
Since now Microsoft has announced that the patch will be released only in January, the company did not meet the deadline, and information about the vulnerability was made public. Stone emphasizes that this decision is dictated by the fact that hackers have already exploited this problem in the past, are familiar with it and can now exploit it again.
Recall that Microsoft was already hastily fixing 0-day vulnerabilities that were already under attack.
And also recall that recently VMware patches 0-day vulnerability discovered by NSA.





