60,000 Android Apps Distributed Adware
Bitdefender analysts found that more than 60,000 Android apps disguised as legitimate products distributed adware, silently installing it on users’ devices.
Moreover, this campaign remained unnoticed by anyone for six months.Let me remind you that we also wrote that Over 1,800 iOS and Android Apps Contain Hardcoded AWS Credentials, and also that Android apps installed 5.8 million times are stealing Facebook users passwords.
Also the media wrote that 151 Android Apps Subscribed Users to Paid Services.
According to the researchers, this campaign has been active since October 2022. The malware is distributed under the guise of security software, cracks and cheats for games, VPN services, hacked versions of YouTube and Netflix, and various utility applications.
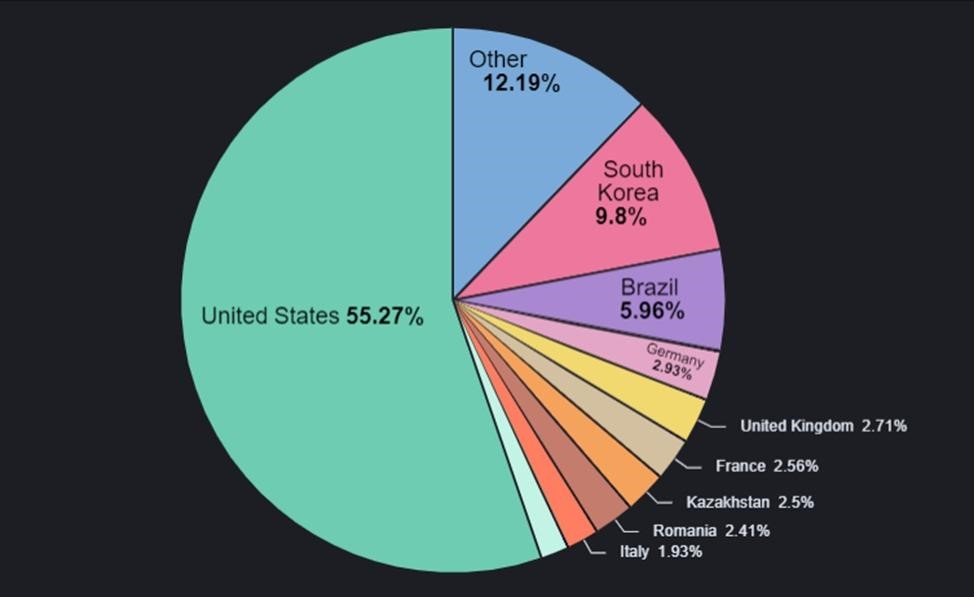
These attacks mainly target users in the US, South Korea, Brazil, Germany, the UK, and France.
Malicious apps are not listed on Google Play, but are distributed through third-party sites in the form of APKs. When visiting these sites, victims are either redirected to sites with advertisements or prompted to download the application they are looking for.
When an application is installed, it does not attempt to sneak into autostart, as this would require additional privileges. Instead, it relies on the normal Android app installation process, which prompts users to launch the app after installing it. Experts note that this is a double-edged sword, because if the user does not launch the application after installation, it will probably not be launched at all.
The report also notes that apps don’t have icons and use UTF-8 characters to make them harder to detect.
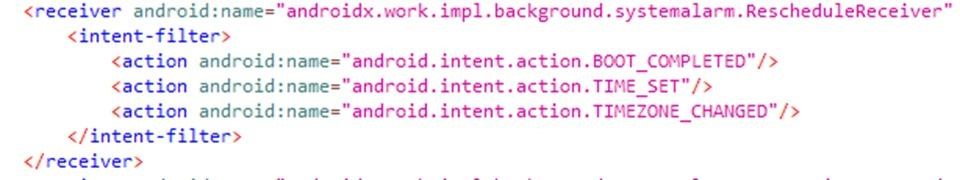
If the victim does launch the app, it will display an error saying that the app doesn’t work in that region, after which the victim will be prompted to click on the “OK” button to delete. In fact, after pressing the button, the application is not deleted, but simply “falls asleep” for two hours, and then registers two intents (intent) that will allow it to run when the device boots or unlocks. Bitdefender notes that last intent is disabled for the first two days, which helps avoid user detection.
As a result, the application communicates with the servers of its operators and receives advertising URLs, which will be used in a mobile browser or as full-screen advertising through WebView.
While the discovered apps are currently being used solely to serve ads, the researchers warn that attackers could replace adware URLs with other malicious sites at any time.





