Security professionals continue to investigate the massive supply chain attack on SolarWinds and its customers. Kaspersky Lab experts have linked the Sunburst backdoor with the Kazuar malware.
Although Kaspersky Lab does not formally participate in the investigation of this incident (and indeed, Russian hackers were accused of the largest attack of 2020), yesterday researchers presented a detailed report on the analysis of the Sunburst malware used in the attack.Let me remind you that in December 2020 it became known that unknown attackers hacked SolarWinds and infected its Orion platform with malware.
“According to official figures, out of 300,000 SolarWinds customers, only 33,000 were using Orion, and an infected version of the platform was installed on approximately 18,000 customers”, – said the researchers.
As a result, the victims included such giants as Microsoft, Cisco, FireEye, as well as many US government agencies, including the State Department and the National Nuclear Security Administration.
In early January, the FBI, NSA, CISA and ODNI issued a joint statement, according to which an unnamed APT group of “probably Russian origin” was behind the massive attack. The SolarWinds hack itself was described by officials as “an attempt to gather intelligence.”
In essence, the agency’s joint statement echoed information released by the Washington Post last December. Then the journalists, citing their own sources, wrote that they associate the attack with the well-known Russian-speaking hack group APT29 (aka Cozy Bear and Dukes), which, according to experts, operates under the auspices of the Russian authorities.
It should be said that experts from FireEye and Microsoft, who studied the incident thoroughly, did not report anything about the possible attribution of the attack. Instead, FireEye assigned the group a neutral codename UNC2452 and said the attack did not specifically target the United States.
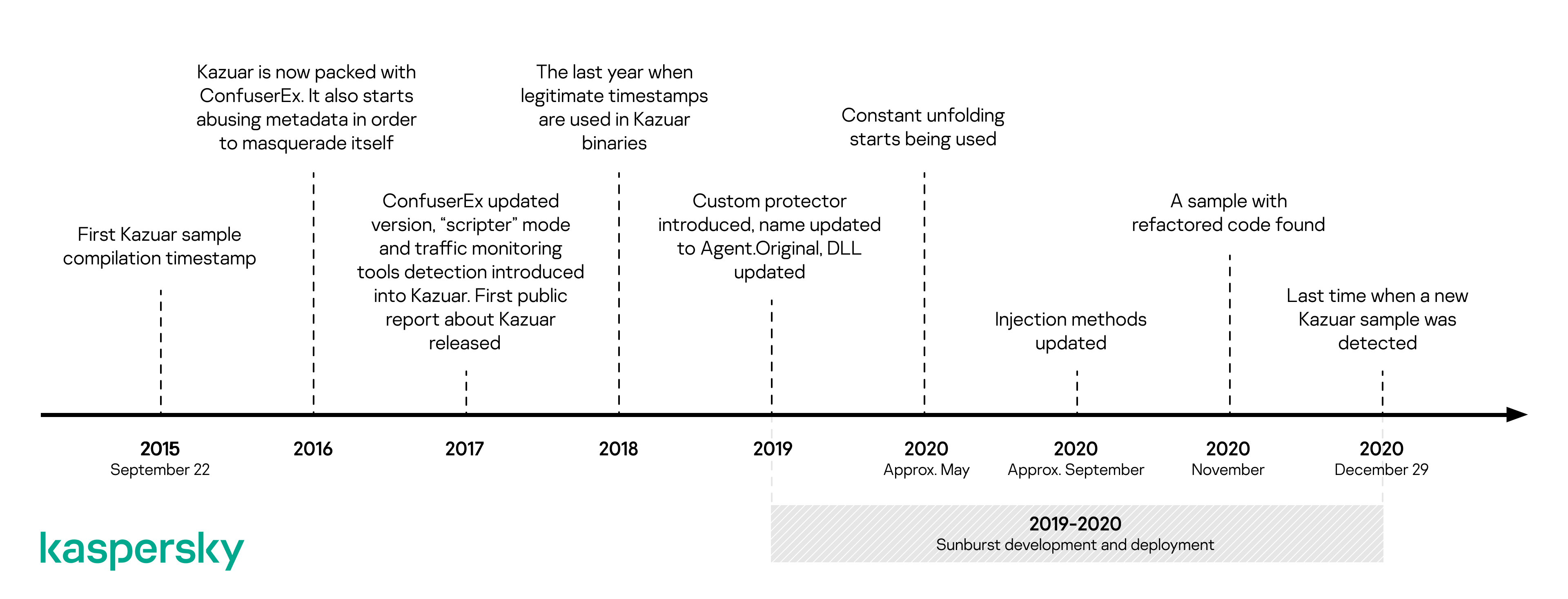
Now experts write that the Sunburst backdoor code is in many ways similar to the .NET Kazuar backdoor, which has long been used by the Russian-speaking hack group Turla (aka Waterbug, Snake, WhiteBear, VENOMOUS BEAR and Kypton). This malware active at least since 2015 and was first described in 2017 by Palo Alto Networks.
The first official mention of the Turla hack group was in 2008 and is associated with the hack of the US Department of Defence. After this incident, for quite a long time it was believed that the group began its activities around 2007, but several years ago, information security specialists discovered traces of Turla in attacks 20 years ago, that is, it is now believed that the group was probably active from the late 90s.
At various times, Turla has been associated with numerous information security incidents – the seizure of satellite communication channels to mask its activities, attacks on government bodies and strategic industries, including the defence industry in Europe, the Middle East, Asia and Africa.
The researchers note that the similarity of the code of the two malwares is not a guarantee that Turla indeed organized the SolarWinds attack. In theory, the similarities could have arisen because the SolarWinds hackers used the same coding ideas or simply bought the malware from the same author. In addition, a malware developer could move from one hack group to another, or a similar code may be a deceptive manoeuvre designed to confuse analysts.
Recall that US authorities have already imposed sanctions on a Russian institution associated with Triton malware.





