Remove Zphs Virus (.[zphc@cock.li].zphs Files Ransomware) – Dharma Ransomware
Zphs – General Info
The Zphs mean a ransomware-type infection. The virus comes from the Dharma ransomware family. Zphs was elaborated particularly to encrypt all major file types. As soon as the file is encrypted people are not able to use them. Zphs adds the “.[zphc@cock.li].zphs” extension for each file encrypted by it. For example, the file “myphoto.jpg“, when encrypted by Zphs, will be renamed into “myphoto.jpg.[zphc@cock.li].zphs“. As quickly as the encryption is completed, Zphs places a special text file into every folder containing the encrypted data.The message given by Zphs text file requesting the ransom is absolutely the same as the statements given by other ransomware virus representatives coming from the Dharma family. It literally discusses that the info is encrypted and that the only way to restore it is to use a a special decryption key. Sadly, this is definitely true. The kind of cryptography mechanism used by Zphs is still not properly examined. Still, it is definitely certain that each victim might be given the specific decryption key, which is absolutely unique. It is impossible to restore the files without the key available.
Another technique of Zphs is that the victims cannot gain access to the key. The key is kept on a particular server run by the frauds related to Zphs ransomware. To get the key and recover the important information people have to pay the ransom.
Zphs encrypted your documents, but that might not be the only damage done to you. The ransomware might still be hidingon your computer. To identify whether this holds true, we suggest downloading GridinSoft Anti-Malware.
Download GridinSoft Anti-Malware
GridinSoft Anti-Malware Review, How to get free trial?, EULA, and Privacy Policy.
Nevertheless, irrespective of the asked for amount, people need to keep away from paying the ransom virus. Cyber frauds are unfair, so they tend to entirely disregard what their victims feel about the problem, even when the payment reaches their pockets. This is why paying the ransom usually does not provide any positive outcome and people simply lose their money for absolutely nothing.
We strongly encourage that you do not contact these crooks and absolutely do not transfer money into their accounts. It is said to admit that there are no utilities able to crack Zphs ransomware and to recover the information data totally free. Therefore, the just best decision is to recover the lost information from the available backup.
Virus Summary
| Name | Zphs Ransomware |
| File Extension | .[zphc@cock.li].zphs |
| Type | Ransomware |
| Family | Dharma |
| Short Description | The ransomware encrypts all the data stored on your system and requires a ransom to be paid on your part supposedly to recover your important files. |
| Symptoms | File encryption by the ransomware is performed by means of the AES and RSA encryption algorithms. Once the encryption is completed, the ransomware adds its special [zphc@cock.li].zphs extension to all the files modified by it. |
| Distribution Method | Spam Emails, Email Attachments |
| Similar Infections | Arena, Wshlp, Nw24 |
| Removal Tool | GridinSoft Anti-Malware |
Keep in mind that the world wide web is now overwhelmed with threats that look similar to Zphs ransomware. It is similar Arena and many other ransomware-type threats. Harmful programs of such kind are usually elaborated to encrypt crucial data and to state the demand before the user to pay the ransom. The peculiarity of all such ransomware threats is that all apply a comparable algorithm to generate the unique decryption key for files decryption.
Thus, as long as the ransomware is still being developed or has some hidden bugs, by hand recovering the information is simply not feasible. The only way to avoid the loss of your crucial files is to regularly create backups of your important information.
Keep in mind that even if you create such backups, they must be placed into a special storage utility not connect to your main computer. You may use the Memory Stick or external hard disk for this purpose, or refer to the help of the cloud storage. If you store your backup files on your common system they may be encrypted along with other files, so it’s definitely not a good storage place.
How did ransomware infect my system?
There are numerous ways used by online scams to distribute Zphs virus. Despite the fact that it doubts how exactly Zphs injects your PC, there are some leaks through which it may infiltrate the system:
- integration with third-party software, especially freeware;
- spam e-mails from unknown senders;
- websites rendering free hosting services;
- pirated peer-to-peer (P2P) downloads.
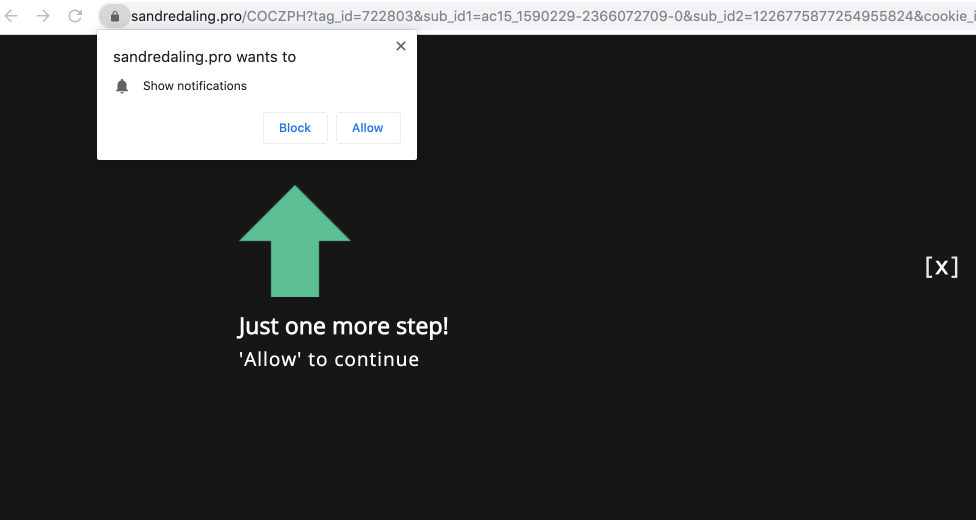
Often Zphs virus may exist as some genuine software, for instance, in the pop-ups advising users to execute some important software updates. This is the common trick used by online scams to persuade people into downloading and installing Zphs infection manually, by means of their direct participation in the installation process.
Furthermore, the criminals might refer to various email spam techniques to inject destructive codes into PC. So, they may refer to to sending unsolicited spam e-mails with tricky notifications promoting users to download the attachments or click on certain download links, for example, the ones motivating users to open some receipts, files, tax reports or invoices.
Needless to mention, opening such documents or clicking on such dangerous links may badly harm the PC. Fictitious Adobe Flash Player upgrade alerts may result in Zphs virus injection. When it comes to the cracked applications, these illegally downloaded programs may also include destructive codes resulting in Zphs secret installation. Finally, injection of Zphs may take place by methods of Trojans that covertly get injected into the system and set up harmful utilities without the user’s consent.
Is there any method to avoid the injection of Zphs ransom virus?
Even though there is no 100% guarantee to avoid your system from getting infected, there are some pieces of recommendations we wish to show with you. To start with, be extremely cautious when you browse the web and particularly while downloading free programs. Stay away from opening suspicious email attachments, especially when the sender of the email is not familiar to you.
Keep in mind that some freeware installers may consist of other unwanted utilities in the package, so they may be destructive. Make certain that your current antivirus software and your entire operating system is always duly updated.
Obviously, downloading pirated software is prohibited and may result in essential damage to be produced your system. Hence, stay away from downloading cracked software. You are likewise highly encouraged to reconsider your existing security software and perhaps change to another security solution that can render much better services of protecting your PC.
Below please find the quotation from the Zphs text file:
Pop-up window: YOUR FILES ARE ENCRYPTED Don\'t worry,you can return all your files! If you want to restore them, follow this link:email zphc@cock.li YOUR ID - If you have not been answered via the link within 12 hours, write to us by e-mail:adresspower@tutanota.com Attention! Do not rename encrypted files. Do not try to decrypt your data using third party software, it may cause permanent data loss. Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam. ---- FILES ENCRYPTED.txt: all your data has been locked us You want to return? write email zphc@cock.li or adresspower@tutanota.com
Screenshot of files with “.[zphc@cock.li].zphs” extension added by the ransomware:
![Zphs Ransomware - encrypt files with .[zphc@cock.li].zphs extension](https://adware.guru/wp-content/uploads/2020/09/Zphs-files-virus.jpg)
Use GridinSoft Anti-Malware to remove Zphs ransomware from your computer
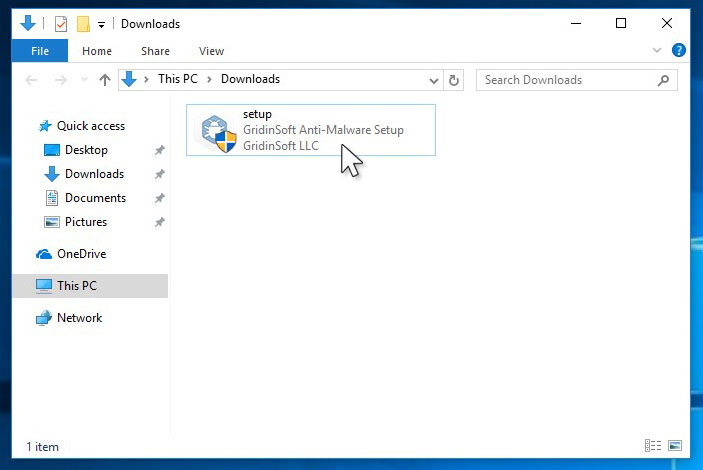
1.Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
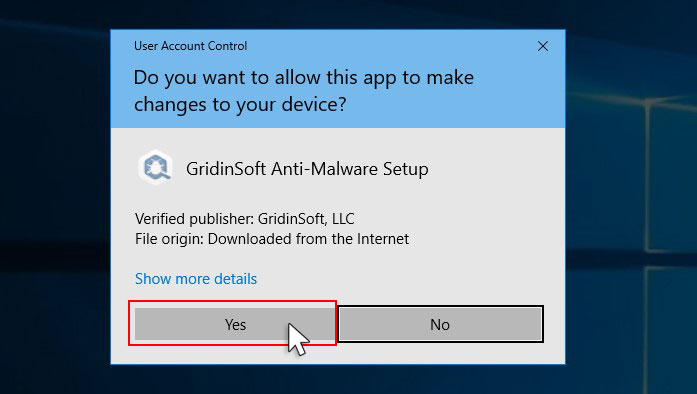
2. Double-click on the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-ag.exe file to install GridinSoft Anti-Malware on your computer.
An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
3. Press Install button for run GridinSoft Anti-Malware.
3.Once installed, GridinSoft Anti-Malware will automatically run.
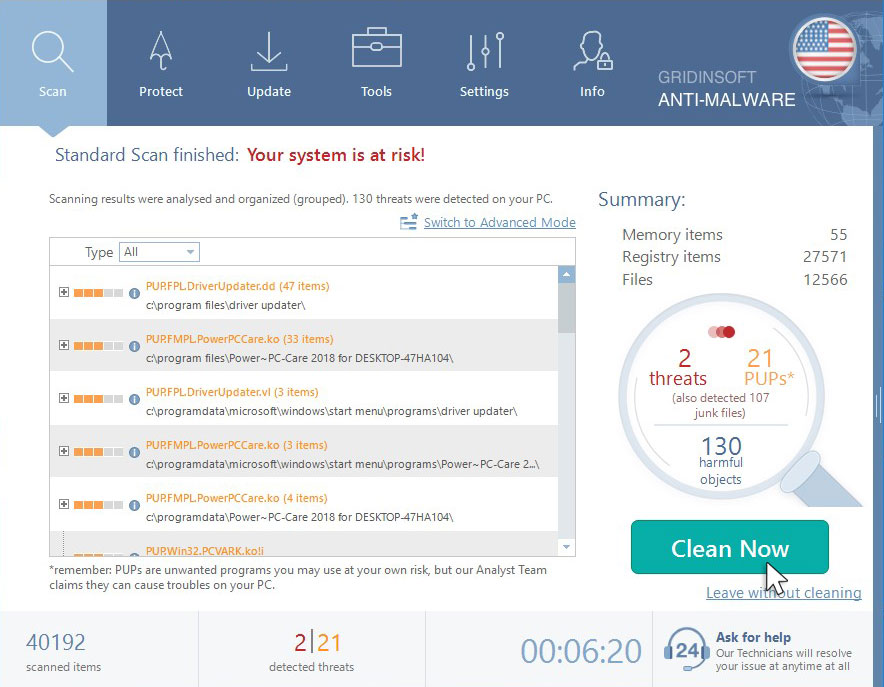
4. Wait for the GridinSoft Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your computer for Win Speedup 2018 and other malicious programs. This process can take a 20-30 minutes, so we suggest you periodically check on the status of the scan process.
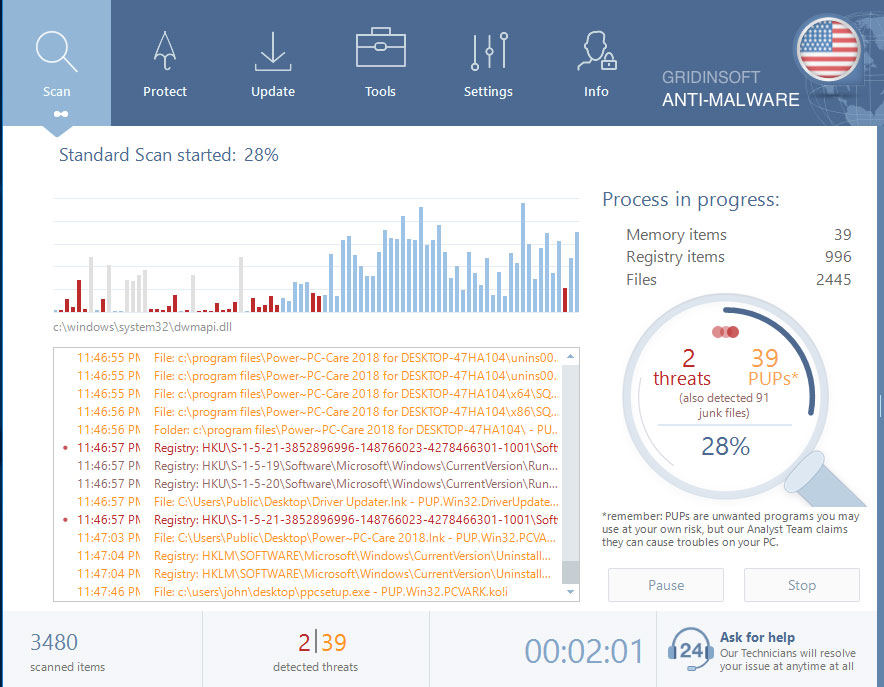
5. Click on “Clean Now”.
When the scan has completed, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.