Netwalker ransomware attacked K-Electric, one of the largest electricity suppliers in Pakistan
Bleeping Computer reports that this week ransomware Netwalker attackerd K-Electric, the largest electricity supplier in the Pakistani city of Karachi, disrupting billing and several other online services.
K-Electric is one of the largest electricity suppliers in Pakistan, serving 2.5 million customers and over 10,000 employees.On September 7, 2020, the company’s customers found they were unable to access online services for their accounts. In an attempt to solve this problem, the specialists of K-Electric redirected users to the staging site, but currently there are difficulties in its operation.
An information security researcher known by the pseudonym Ransom Leaks, who told journalists about the incident, reports that according to a local Pakistani information security company, this attack affected the internal services of K-Electric, but did not affect the supply of electricity.
BeepingComputer also cites its own anonymous sources in the cybersecurity community, which claim that K-Electric has become a victim of the Netwalker ransomware. For example, journalists cite screenshots of the cybercriminals’ Tor payment site, where ransomware operators demand from K-Electric representatives $3,850,000 in cryptocurrency ransom. If the ransom will not be paid during the next week, the attackers promise to increase the amount to $7.7 million.
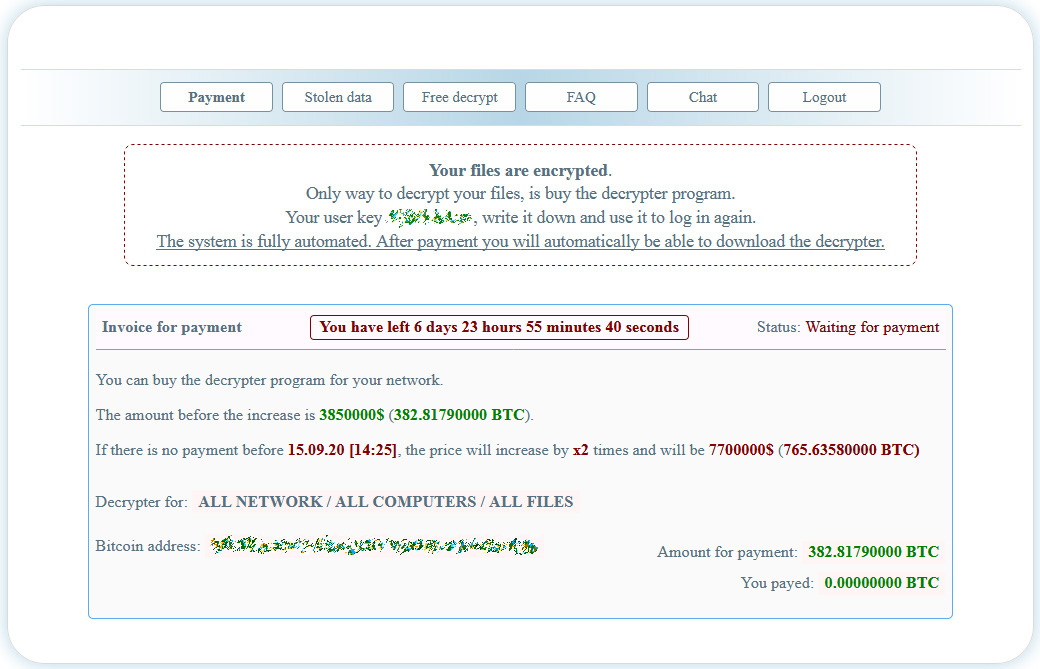
In addition, hacker’s site also has a link to the Stolen data page, where Netwalker operators claim to have stolen some files from K-Electric before carrying out the attack. It is not yet known exactly what information and to what extent the attackers could have stolen, but the hackers threaten to disclose the files in 20 days if the company does not pay.
The NetWalker ransomware was first detected in August 2019. It was originally named Mailto, but later the researchers renamed it NetWalker.
The malware works according to the RaaS (ransomware-as-a-service) model: attackers register on a special portal and undergo testing, after which they can create their own versions of the ransomware.
American law enforcement and information security experts note that in recent months the group’s activity has increased significantly. Currently, the most famous victims of NetWalker are the University of California, San Francisco (UCSF) and the University of Utah, infected by the ransomware this summer.
According to McAfee experts, NetWalker can be compared to Ryuk or REvil in terms of “profitability”, as since March 2020, the ransomware has brought its operators about $25,000,000.