Chinese Hack Group Twisted Panda Spies on Russian Defence Developments
According to Check Point experts, Chinese hack group Twisted Panda attacked at least two research institutes in Russia and a third “probable facility” in Belarus. The group is associated with other Chinese attackers, including Stone Panda (aka APT 10, Cicada or Potassium) and Mustang Panda (aka Bronze President, HoneyMyte or RedDelta).
To balance the news, we will inform you that Russian Hackers Planned to Disrupt Eurovision 2022, and also that Russian Hackers Launched a Massive Spear-Phishing Campaign.The researchers write that they have uncovered this long-term spy operation directed against organizations associated with Russia. This malicious campaign has been active since at least June 2021, and the last traces of hacker activity were discovered as recently as April 2022.
The targets of the Twisted Panda attacks were two unnamed defense research institutes related to the state corporation Rostec, as well as an unknown company from Minsk.
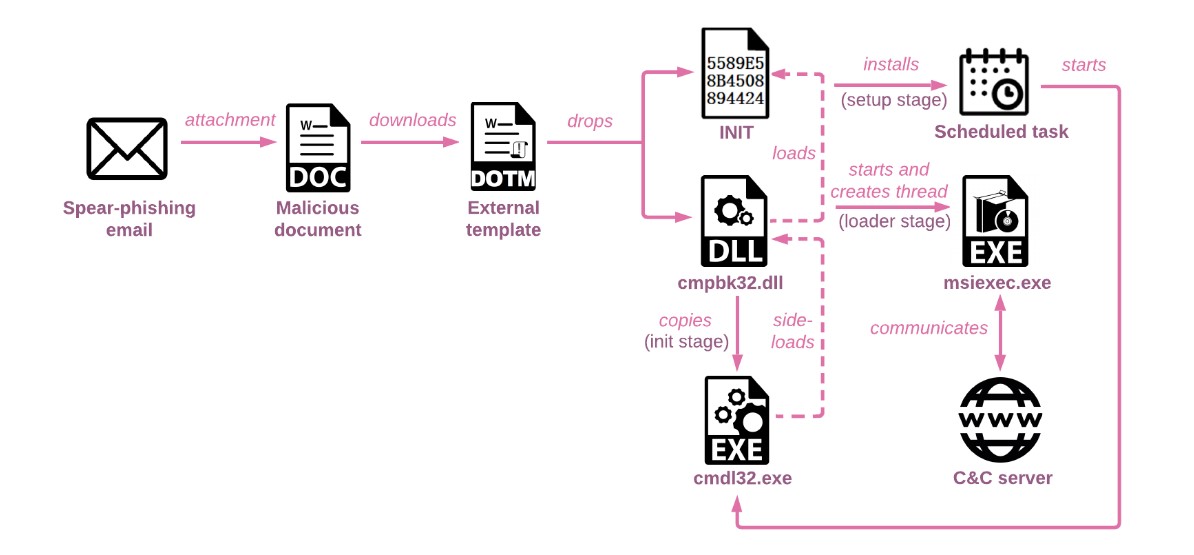
The attacks began with phishing emails containing a link disguised as the website of the Russian Ministry of Health, and in the subject line of the emails the hackers misused the question “special operation” in Ukraine. In fact, such links led to a domain controlled by the attacker and to a fake Microsoft Word document that was intended to trigger the deployment of the downloader.
Then, a DLL library (cmpbk32.dll) was delivered to the victim’s machine, which provided the malware with a permanent presence in the system (using a scheduled task), and was also responsible for executing the second stage multi-level loader, which was subsequently unpacked to deliver the final payload.
The embedded payload itself was a previously undocumented spinner backdoor. According to experts, he uses sophisticated methods, including control flow flattening, to hide his activity. Previously, already mentioned Stone Panda and Mustang Panda groups used such methods in their attacks.
At the same time, despite the complex code structure, Spinner is a basic malware that is used only to account for compromised hosts and launch additional payloads received from a remote server.



