The malware was hiding in several applications hosted on the Google Play Store. During the months during which the program went unnoticed, hundreds of users managed to infect their devices.
As representatives of the Motherboard found out, this Android-malware was sold to the Italian authorities by a company engaged in the development of surveillance cameras. Experts say that the program could hit completely innocent people, because the authors did not figure out how to correctly target it.
Experts also tend to believe that this spyware program is illegal. Most of them once again pay attention to the fact that all protective measures of the Google Play Store at this stage can be circumvented.
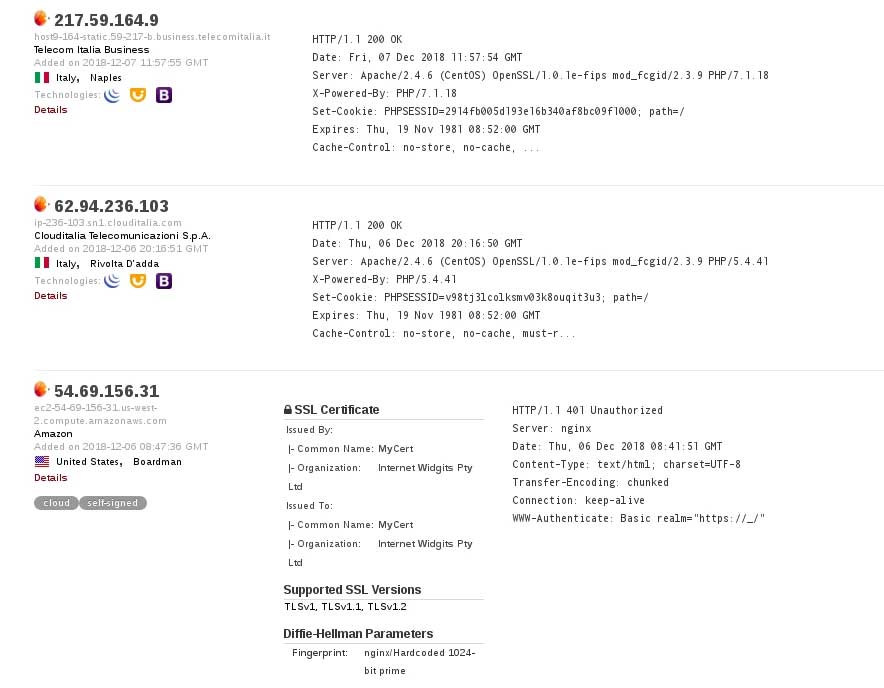
The malicious program, trying to mislead users, tries to look like a completely safe application. For example, versions that were disguised as special offers from Italian telecom operators were noted.
Experts called this program Exodus. Once installed, the Exodus system checks the phone number and IMEI of the device. The malware then initiates the download of a ZIP file, which stores a program that cracks the phone and steals user data.
Exodus is interested in audio recording of everything that surrounds the device you are listening to, recording calls, browser history, calendar information, geolocation, Facebook Messenger logs, WhatsApp chats, and SMS messages.
At the time of publication, the Italian State Police did not respond to multiple requests for comment on the technology subject to their tender, nor they had replied to questions on the use of this spyware. Questions to two Italian Public Prosecutor’s Offices went unanswered as well.
The police agent agreed that eSurv’s spyware lacked the right scope and safeguards to ensure it wouldn’t hit people who were not being under investigation.
Source: https://motherboard.vice.com



