Researchers stumbled upon several samples of malicious .dmg files that are used in the macOS system. They were disguised as installation files of various popular programs and were distributed on torrent sites.
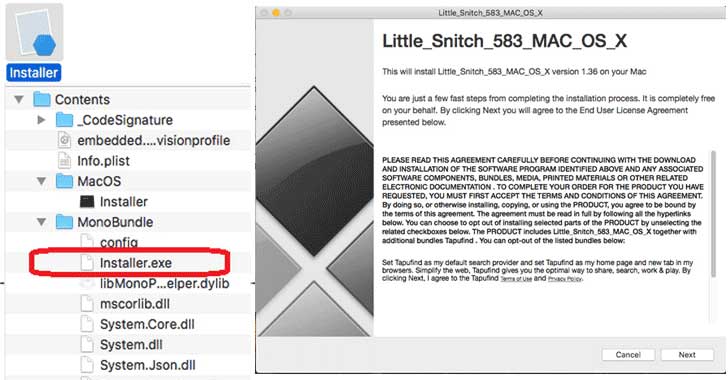
What is most interesting is that these samples included an EXE application compiled using the Mono framework, which makes files of this format compatible with macOS. Mono is an open source implementation of the Microsoft .NET Framework that allows developers to create cross-platform programs.
Usually EXE files when trying to run on macOS give an error. Another important fact is that security features like Gatekeeper do not scan .exe files for malicious code. Fake installer, discovered by experts, is disguised as an installation file from the Little Snitch firewall:
During the installation process, the malware prompts the user to install an advanced set, some of which are disguised as Adobe Flash Media Player and Little Snitch. Experts could not identify any specific pattern of these attacks.
… We suspect that this specific malware can be used as an evasion technique for other attack or infection attempts to bypass some built-in safeguards such as digital certification checks since it is an unsupported binary executable in Mac systems by design. We think that the cybercriminals are still studying the development and opportunities from this malware bundled in apps and available in torrent sites, and therefore we will continue investigating how cybercriminals can use this information and routine. Users should avoid or refrain from downloading files, programs, and software from unverified sources and websites, and install a multi-layered protection for their individual and enterprise systems.
Trend Micro Solutions



