News
-

June patch does not fully fix 0-day vulnerabilities in Windows
In May 2020, Trend Micro Zero Day Initiative researchers reported about five unpatched 0-day vulnerabilities in Windows, four of which…
Read More » -

Let’s Encrypt developers solved the problem of old Android devices
In the fall, Let’s Encrypt developers warned that in 2021, users of devices running Android 7.1 (Nougat) and older versions…
Read More » -

MageCart malware operators accidentally disclosed addresses of hacked stores
Sansec experts noticed that the dropper of an unnamed hack group that is infecting MageCart online stores with malware (web…
Read More » -

Addresses of 270,000 Ledger crypto wallet users leaked to the network
Bleeping Computer reports that email addresses and physical addresses of 270,000 Ledger hardware wallet users have leaked into the network.…
Read More » -
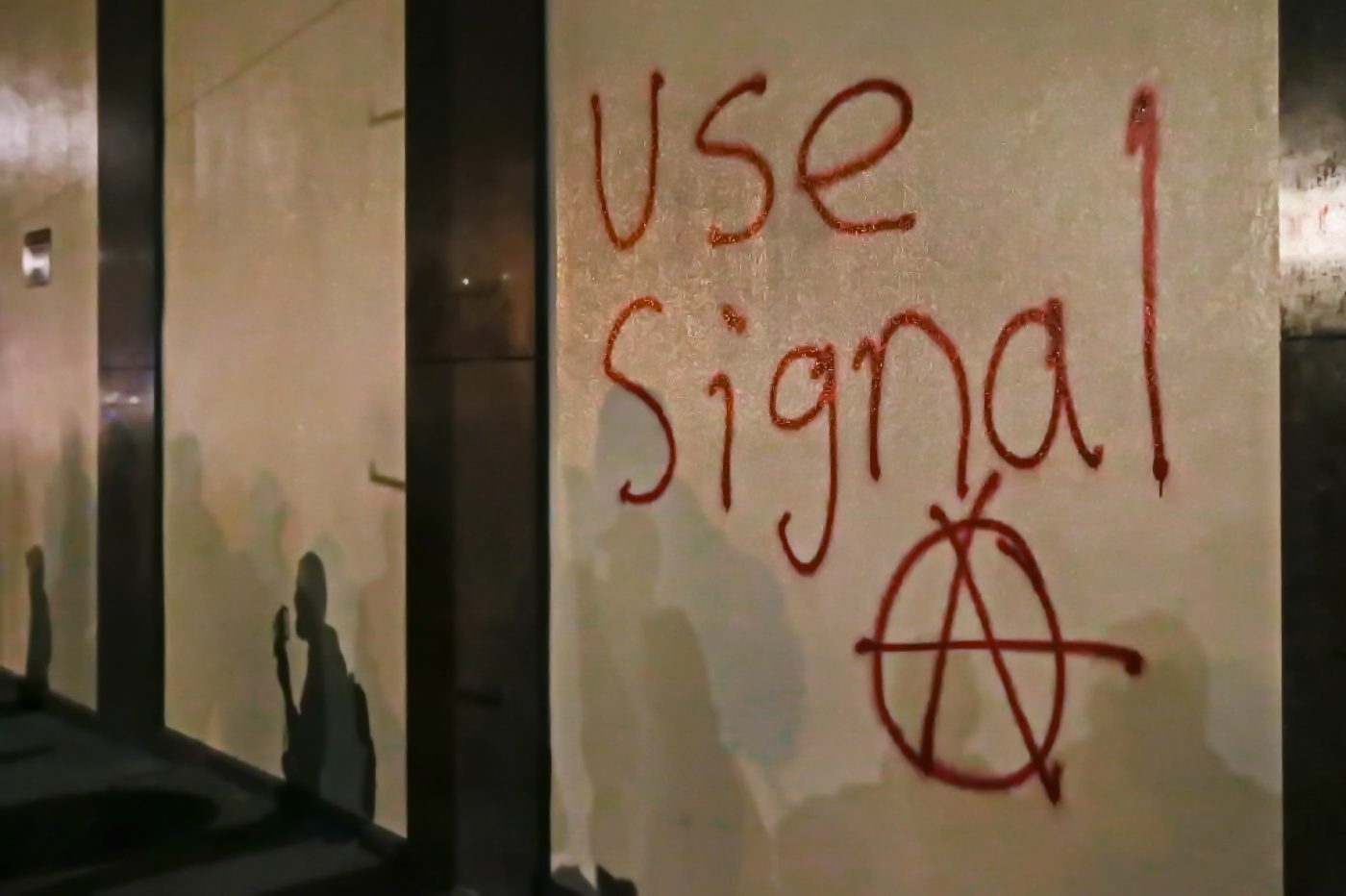
Cellebrite says it can now hack the Signal messenger
Mobile hacking tool maker Cellebrite, an Israeli company, said its tool can now hack the Signal app, which is considered…
Read More » -

Hackers Influenced Valve’s Online Games Using Vulnerabilities in the Steam Platform
The Check Point team has discovered vulnerabilities in the Steam gaming platform from Valve. The root of the problem lay…
Read More » -

Hackers exploit vulnerability in Easy WP SMTP WordPress plugin to reset admin passwords
Last week, the popular Easy WP SMTP plugin for WordPress, installed more than 500,000 sites, was patched for a serious…
Read More » -

Attackers hide MageCart scripts even in CSS files
Over the years, hacker groups have come up with a variety of tricks to hide their web skimmer code from…
Read More » -

D-Link developers fixed serious bugs in their routers
In the summer of this year, Digital Defense specialists discovered quite serious bugs in a number of D-Link router models.…
Read More » -

DoppelPaymer ransomware attacked Foxconn Mexican division
Bleeping Computer reported that two weeks ago, on Thanksgiving Day, the DoppelPaymer ransomware attacked Foxconn Mexican division. Attackers demand from.…
Read More »