Thanos ransomware tries to overwrite MBR
Palo Alto Networks specialists noticed that Thanos ransomware has acquired new functionality and is trying to overwrite the MBR (Master Boot Record) on infected machines in order to prevent the system from starting normally.
In particular, this behavior of the malware was recorded in July 2020, during two attacks on government agencies in the Middle East and North Africa. Fortunately, the malware authors made a mistake in the code, and the MBR of the affected systems remains intact.“Overwriting the MBR is a more destructive approach to ransomware attacks. Victims will have to work harder to recover their files, even if they pay the ransom. Fortunately, in this case, the code responsible for rewriting the MBR did not work because the ransom message [to be displayed on the lock screen] contained invalid characters”, — said analysts from Palo Alto Networks.
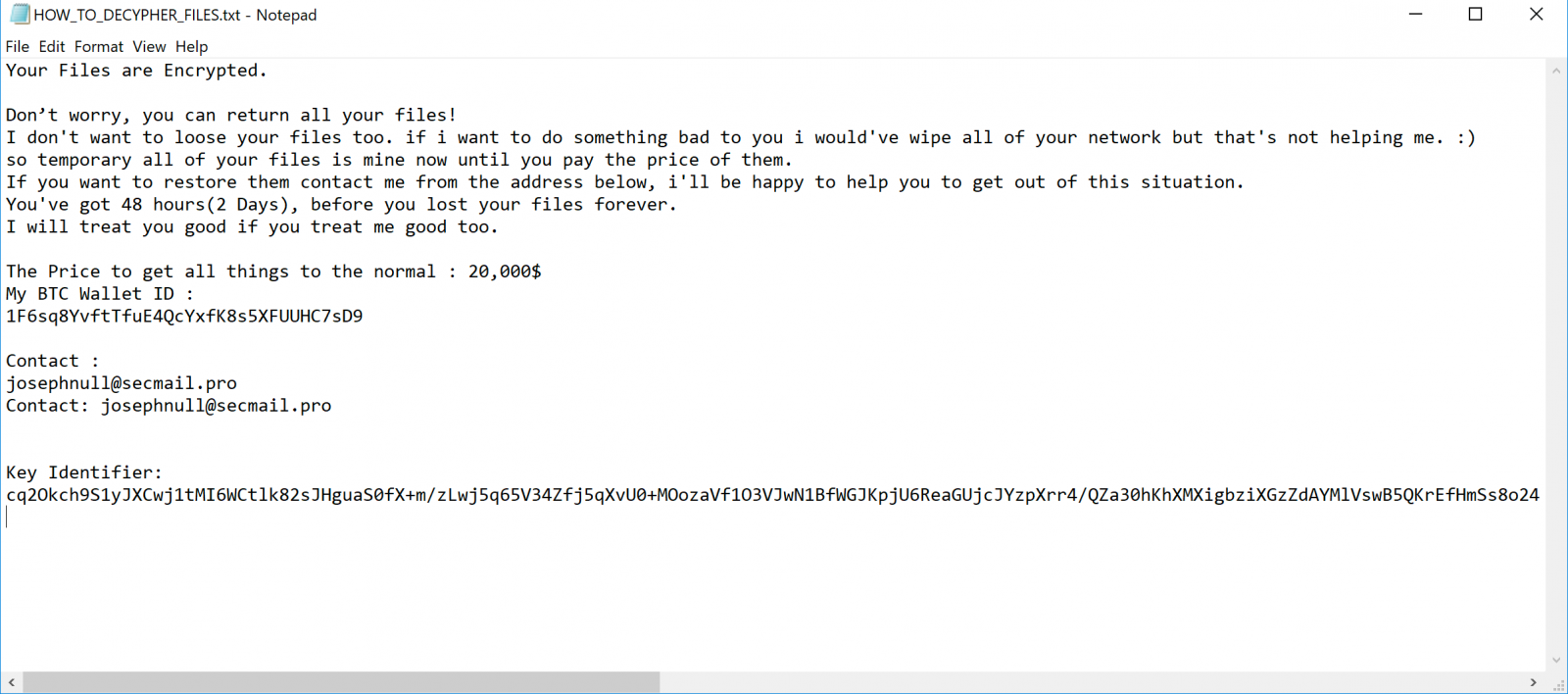
Although the malware failed to overwrite the MBR, during these attacks, Thanos operators created plain text files HOW_TO_DECIPHER_FILES.txt on infected machines and demanded $ 20,000 from their victims for data recovery. At the same time, the experts have no information about whether the victims agreed to pay the ransoms.
Researchers believe that attackers infiltrated targeted networks long before deploying the ransomware payloads, as valid credentials were found in samples recovered from the attack.
Thanos is a RaaS (Ransomware-as-a-Service) that has been actively advertised on Russian-language hacker forums since February 2020. Some of the Thanos samples also featured in expert reports called Hakbit (due to the various extensions the ransomware leaves behind), but researchers at Recorded Future write that it was the same malware.
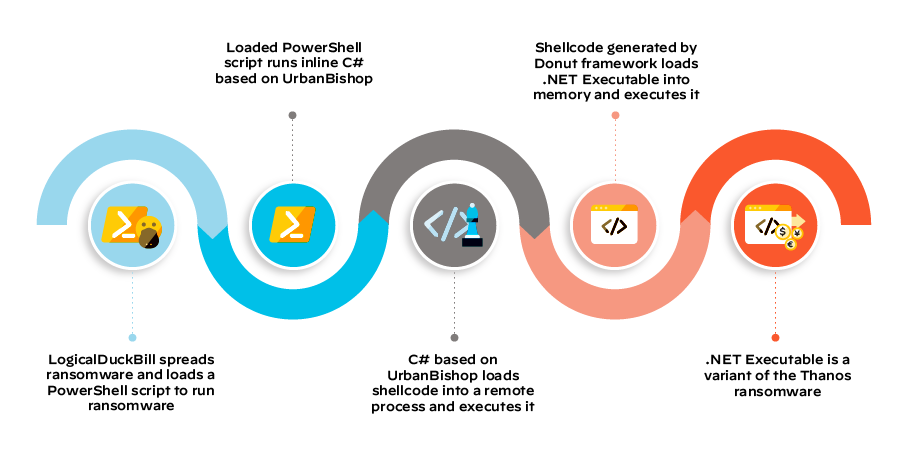
Although Thanos ransomware is not new, it looks like it is still in active development, as the version used in these attacks, according to the observations of Palo Alto Networks experts, contained new features. New functionality included the ability to detect and evade additional analysis tools, enumerate local storage volumes using the method used by the ransomware Ragnar Locker, and a new ability to track newly attached storage devices.
Let me remind you though the era of Thanos has not come yet, we are definitely experiencing the peak of activity of other ransomwares. For example, recently RansomEXX attacked Konica Minolta, and Conti ransomware got its own website for stolen data like their colleagues from Maze Cartel.
Take care please.



