SolarWinds Hackers Spread NativeZone Backdoor
Microsoft said the Russian hacker group behind the SolarWinds attack has attacked the US Agency for International Development. Hackers used the NativeZone backdoor and four new malware families in the campaign.
The researchers attribute the discovered attacks to the Russian-speaking hack group APT29 (aka Cozy Bear, Dukes, Nobelium), which, according to experts, operates under the auspices of the Russian authorities.Researchers report that hackers compromised AMP’s Contact Contact account and then used that account to impersonate agency representatives in phishing emails that appeared to be authentic.
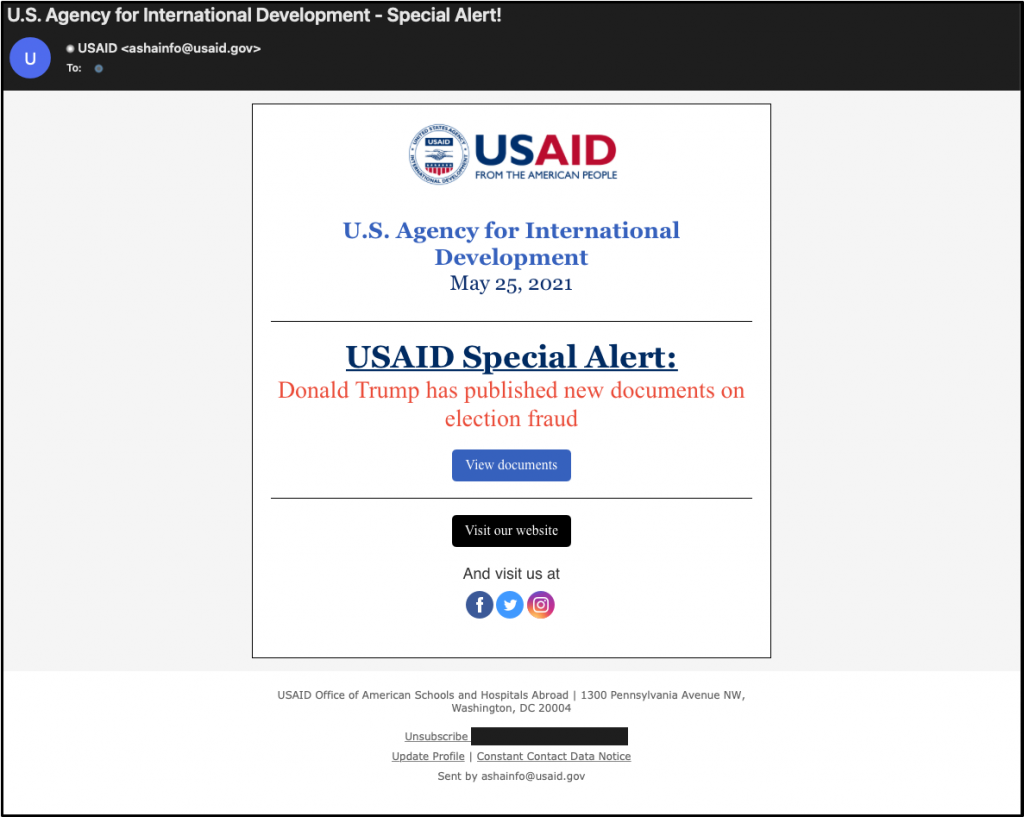
In total, the attackers sent such messages to approximately 3,000 accounts in more than 150 different organizations, including government agencies and organizations involved in international development, humanitarian and human rights activities. The last wave of these attacks began on January 28, 2021, and intensified markedly on May 25.
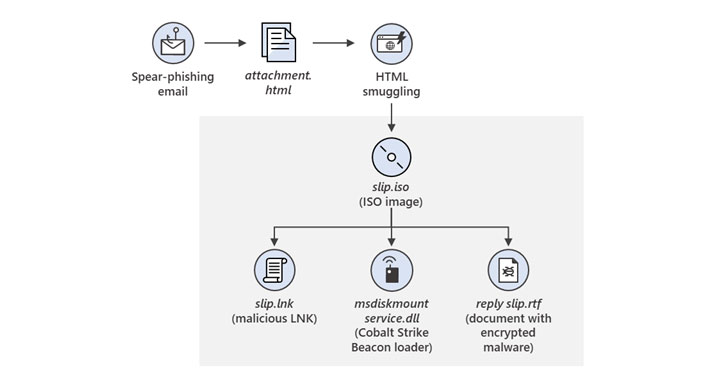
Sometimes phishing emails contained a link that, when clicked, delivered the malicious ICA-declass.iso file, which was used to deploy the Cobalt Strike beacon dubbed NativeZone (Documents.dll). This backdoor can be used for permanent system access, lateral movement, data extraction and additional malware installation.
If the victim’s base operating system was iOS, it was redirected to another remote server with an exploit for the zero-day vulnerability CVE-2021-1879. However, Apple addressed this flaw at the end of March, admitting that the problem could have been exploited by hackers.
Microsoft also released details on four new malware families used by Nobelium in these attacks: an HTML attachment called EnvyScout, a BoomBox downloader, a NativeZone backdoor downloader, and a VaporRage tool designed to download and run shellcode.
Let me remind you that we wrote that Chinese hackers also took part in attacks on SolarWinds clients, as well as that SolarWinds Attack Gives Hackers Access to Trump Administration Officials Accounts.