Samsung Galaxy S22 Hacked on Pwn2Own
Toronto hosts the annual Pwn2Own hacking competition — during the first day, participants successfully hacked a Samsung Galaxy S22 smartphone twice.
This year, as part of the Pwn2Own Toronto 2022 competition organized by the Trend Micro Zero Day Initiative (ZDI), researchers can prove themselves in attacks on mobile phones, printers, wireless routers, NAS, smart speakers, smart home hubs and other devices, which are updated to the latest versions and work with default settings.The most valuable prizes can be earned in the category of mobile phones: up to $200,000 for hacking Google Pixel 6 and Apple iPhone 13 smartphones. There are also $50,000 bonuses for hacking Google and Apple devices if exploits are executed with kernel-level privileges. Thus, the maximum reward is $250,000 for a full chain of exploits with access at the kernel level.
This time, Pwn2Own Toronto has been extended to four days, as 26 teams take part in the competition at once, which intend to attack 66 targets in all declared categories.
During the first day of the competition, experts from the STAR Labs team were the first to demonstrate exploitation of a zero-day vulnerability on a Samsung flagship device. On their third attempt, they carried out an input validation attack, and the hack netted the team $50,000 and 5 Master of Pwn points.
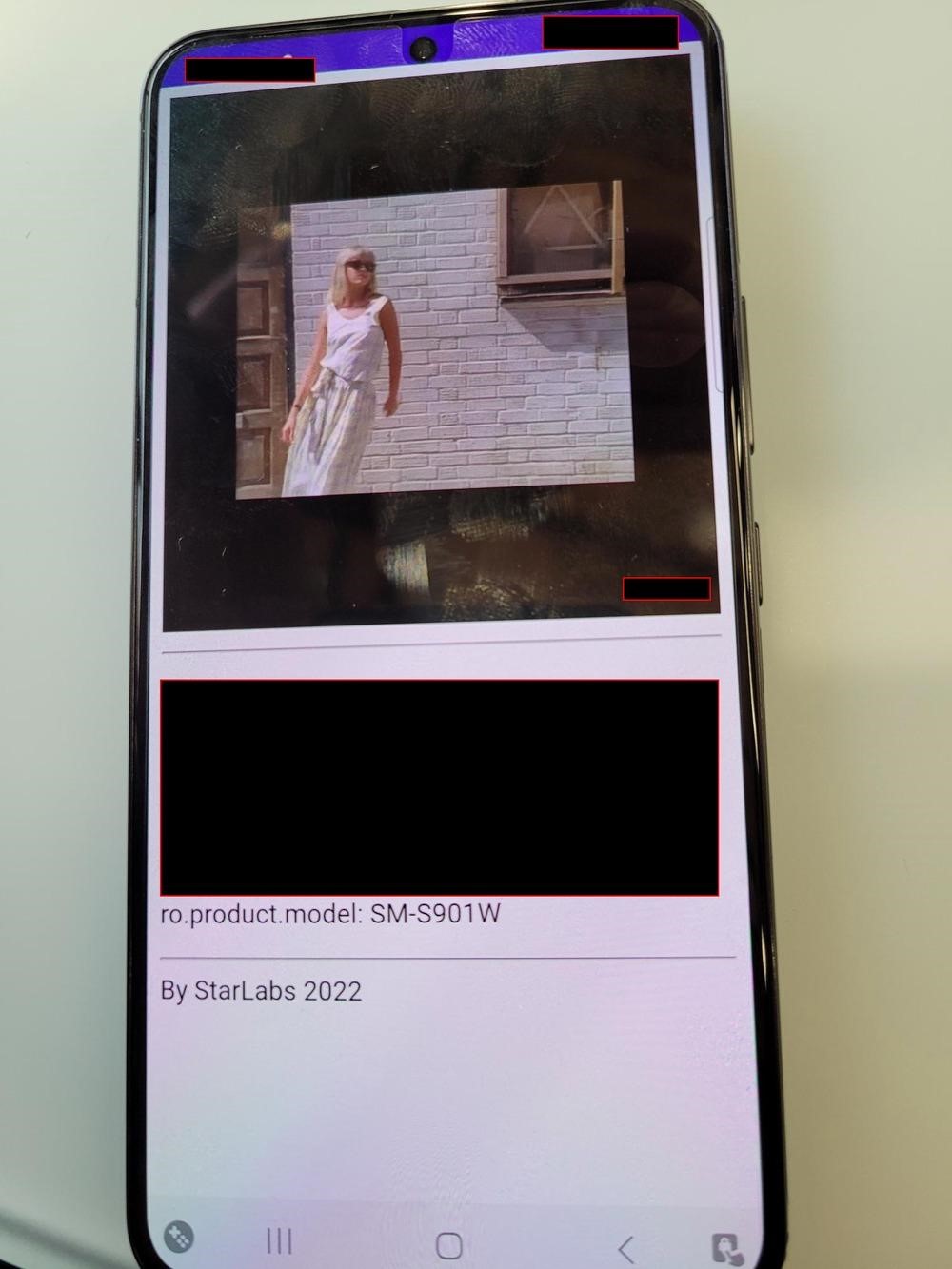
Another contributor, Chim, also showed a successful attack on a Samsung Galaxy S22, and was able to perform an attack that also involved incorrect input validation. This earned him $25,000 (50% of the prize for the second round of attack on the same device) and 5 Master of Pwn points.
By the way, did you know that US authorities can hack iPhone, but may have difficulties with Android?
Also during the first day of the competition, participants demonstrated working exploits for 0-day vulnerabilities in printers and routers from several vendors at once, including Canon, Mikrotik, NETGEAR, TP-Link, Lexmark, Synology and HP.
The largest award of the first day went to the Devcore team, which has taken part in Pwn2Own competitions more than once in past years. Experts earned $100,000 for hacking a MikroTik router and a Canon printer connected to it.
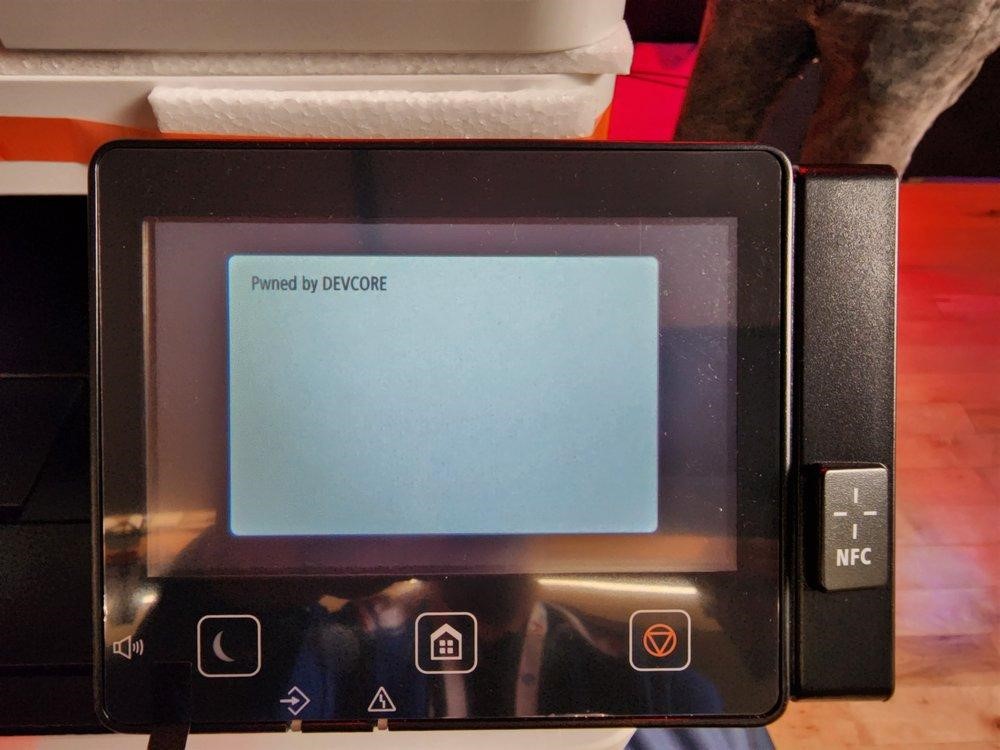
This attack was introduced in Pwn2Own’s new SOHO Smashup category. In this category, researchers are asked to hack into an environment that mimics a typical home office. In essence, the goal is to hack the router through the WAN interface and then go to the local network, where you will need to compromise any other device of your choice (for example, a printer, NAS, and so on).
The Neodyme team was also successfull in the SOHO Smashup category, earning $50,000 for hacking a Netgear router and HP printer.
By the way, we also wrote that Pwn2Own members made the printer to play AC/DC.
Researchers at industrial security and IoT company Claroty earned $40,000 for hacking a Synology DiskStation NAS.
Also, several rewards in the amount of $20,000 were received by experts for hacking Canon, HP and Lexmark printers, as well as TP-Link and Synology routers. The two teams earned $10,000 each for hacking Synology NAS and HP printers.



