Foty Virus Removal Guide (+Decrypt .foty files)
Foty – Ransomware
Foty is a destructive software application working as common ransomware. Michael Gillespie, the widely known malware researcher, first discovered this new name in the DJVU ransomware family.
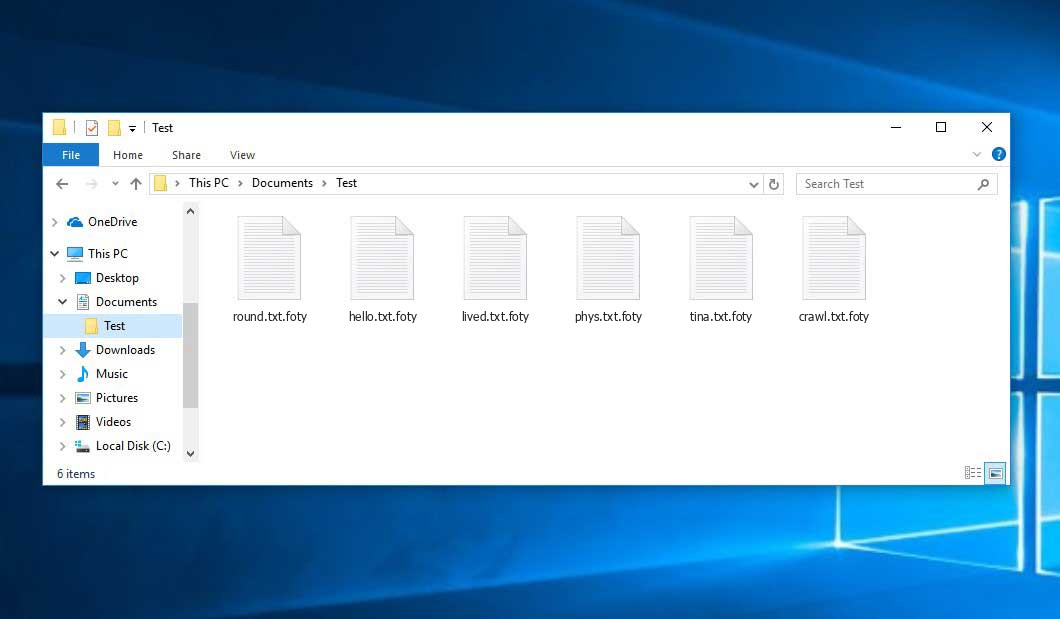
Foty was developed for the sole purpose to encrypt all popular file types. Realistically, as soon as the encryption is effectively accomplished, the users are not able to get access to them. Foty ransomware includes its own “.foty” to all the encrypted data. For instance, the file “price_list.xls”, as soon as crypted by Foty, will be entitled as “price_list.xls.foty”. As soon as the file encryption is accomplished, Foty puts its own distinct text file (_readme.txt) into all the folders that keep the encrypted files.
The message specified by document requesting the random os very similar to the notifications offered by other ransomware risks coming from the DJVU family. The warning generally shows that the data has been encrypted and the only option to get access to it is to use a distinct standalone key. Regretfully, this declaration is definitely true.
The technique to secure the files utilized by Foty is not completely researched. Nevertheless, there is no doubt that each computer owner might be issued an unique decryption key, which is absolutely unique. It is very tough to recuperate the information without the appropriate key in place.
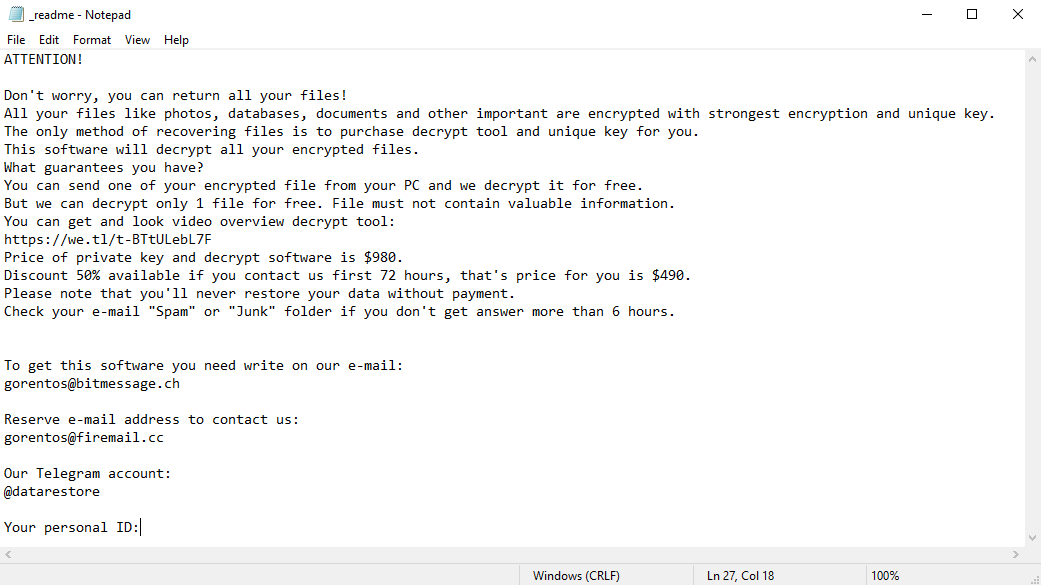
“Don’t worry, you can return all your files!”, from text file message:
One more peculiarity of the Foty ransomware is that the users are not able to get access to the key. The decrypting key is hosted on a special server under the complete control by the criminals who have actually released the Foty virus into the world wide web. In order to obtain the key and restore the crucial information, the users are told to contact the frauds by means of email or by telegram and to pay the ransom in the amount of $980.
The message likewise says that individuals need to get in touch with the Foty authors within 72 hours upon the minute of the data encryption. The alert indicates that by doing so the people will obtain a 50% discount rate, therefore, the ransom amount falls to $490.
Foty crypted your data, however, it might not be the only threat on your computer. Plus, the ransomware might be concealed deep in the system. To identify and delete the threat completely, we suggest you to refer to the aid of GridinSoft Anti-Malware app.
Download GridinSoft Anti-Malware
GridinSoft Anti-Malware Review, How to get free trial?, EULA, and Privacy Policy.
No matter what the amount of the ransom is, we highly encourage that you do not pay the ransom. There is no assurance that these online scoundrels will keep their promises, so they might not care at all what the victims feel about the encryption, even when the amount of the ransom is received into their accounts. Thus, paying ransom frequently does not lead to an effective healing. So, the users may just lose their money for absolutely nothing.
Similarly, we advise you not to contact the scams as they advise. Do not transfer loan into their wallets. There are no applications that could split the Foty virus or bring back the information for free. For that reason, the only appropriate choice is to restore the data from possible backups (if offered).
Virus Summary
| Name | Foty Ransomware |
| File Extension | foty |
| Type | Ransomware |
| Family | DJVU |
| Short Description | The ransomware encrypts all the data stored on your system and requires a ransom to be paid on your part supposedly to recover your important files. |
| Symptoms | File encryption by the ransomware is performed by means of the AES-256 algorithm (CFB mode) encryption algorithm. Once the encryption is completed, the ransomware adds its special .foty extension to all the files modified by it. |
| Distribution Method | Adware bundles and software cracks |
| Similar Infections | Lokas, Besub, Nusar |
| Foty Removal Tool | GridinSoft Anti-Malware |
| Foty Decryption Tool | Emsisoft Djvu Decryptor |
Do not forget that the Internet is now full of infections similar to the Foty virus. For instance, this particular threat is basically identical to Brusaf and other ransomware-type infections. These destructive utilities have actually been established in order to secure the crucial data and express the demand for the users to pay the ransom. All these infections utilize the similar algorithm to create the particular key for effective files decryption.
Unless the Foty ransomware is still under the advancement process or has got some concealed bugs, it is not possible to restore the data by hand. Hence, the only working solution to avoid the loss of your important information is to routinely preserve up-to-date backups of all your important files.
Another important piece of advice is to save the backups on special storage not connected to your main computer. For instance, you may store it on the USB Flash Drive, or some external drive, or by using the cloud data storage services. Keeping the backups on your regular drive is very dangerous, given that the backup may also be secured by the Foty ransomware.
Leaks for the Foty ransomware attack.
Foty uses many paths to penetrate the susceptible computers. It is not particular what specific approach was used in your case, nevertheless, the invasion might happen by means of the following channels:
- bundling with third-party programs, primarily freeware;
- spam emails from the unknown senders;
- sites supplying free hosting;
- P2P (peer-to-peer) torrent downloads.
There are times when the Foty might camouflage itself as some authentic application, for example, through the deceptive alerts demanding setup of some software application upgrade. This is the most common trick utilized by the frauds to inject the Foty virus files into the system. By doing this users partly participate in its setup, without plainly understanding the threat.
Additionally, the scams may send unsolicited spam e-mail with difficult alerts encouraging individuals to open dubious accessories or click on some download links, for instance, those encouraging the people to open certain images, text files, tax documents and other information.
No doubt, opening these files or clicking the harmful links may essentially damage the system. Fake Acrobat Reader update notices may lead to the Foty ransomware infiltration. Likewise, downloading the split software may in addition contain the ransomware installer. The last however not the least, installation of Foty might occur through some Trojan horses that may be set up stealthily into the system and without the user’s direct approval or even permission.
Avoiding the Foty ransomware attack.
Obviously, there is no outright assurance that your computer system will be constantly without any malware attacks, however, we want to share some helpful tips with you to make it more secure. Make sure to pay very attention while browsing the web and specifically while getting cost-free programs. Do not open any suspicious email attachments, especially if the sender is not understood to you.
Do not forget that specific freeware installer might likewise include some other additional apps in the bundle. These additional applications might be extremely destructive. It is of utmost value to keep your anti-virus software application and your os in general to be always properly updated.
It is quite logical that downloading pirated apps is illegal, nevertheless, in addition, such unauthorized apps usage may also bring severe damage to your computer. Hence, do not download any broken programs. Plus, the reality that your current anti-virus did not protect the system from the Foty ransomware is a great factor for you to reassess your options and change to another program that can render the securing functions on a much better level.
Below please find the quotation from the Foty text file:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-2P5WrE5b9f Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: restorealldata@firemail.cc Reserve e-mail address to contact us: gorentos@bitmessage.ch Our Telegram account: @datarestore
Screenshot of files with “.foty” extension added by the ransomware:”
Use GridinSoft Anti-Malware to remove Foty ransomware from your computer
1.Download GridinSoft Anti-Malware.
You can get GridinSoft Anti-Malware by clicking the button below:
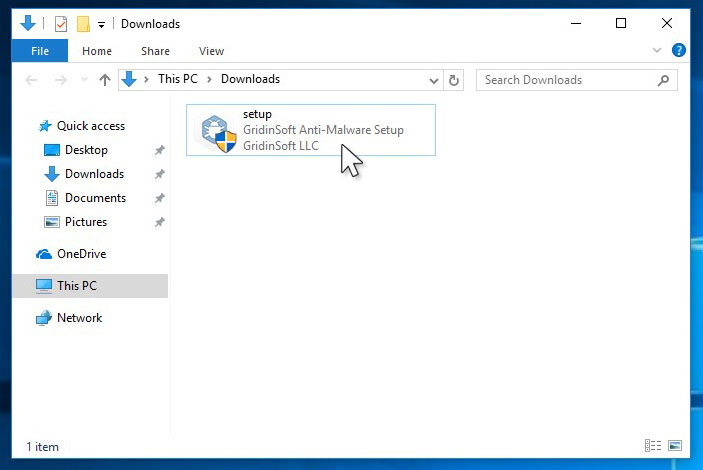
2. Double-click on the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-ag.exe file to install GridinSoft Anti-Malware on your computer.
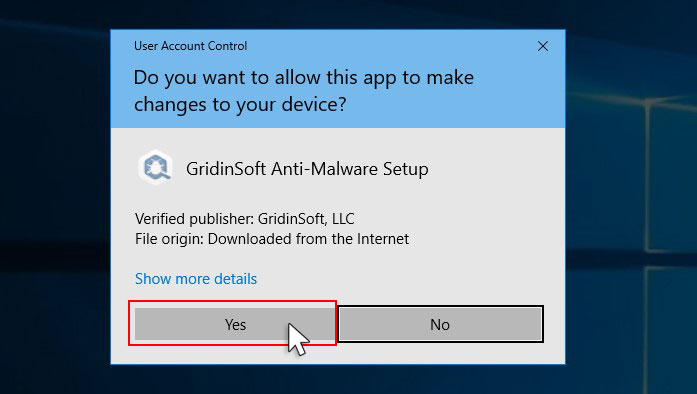
An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
3. Press Install button for run GridinSoft Anti-Malware.
3.Once installed, GridinSoft Anti-Malware will automatically run.
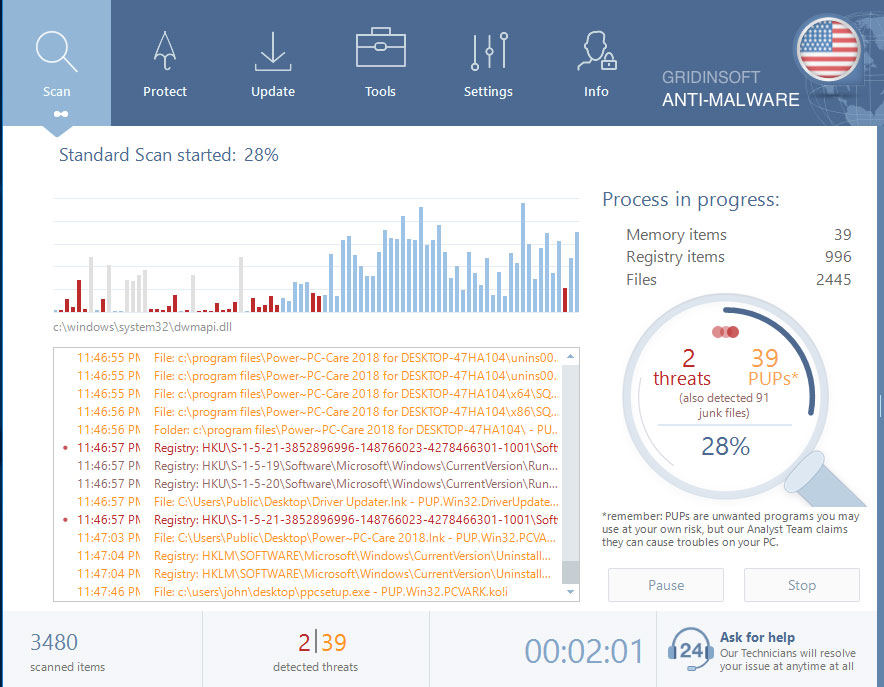
4. Wait for the GridinSoft Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your computer for Win Speedup 2018 and other malicious programs. This process can take a 20-30 minutes, so we suggest you periodically check on the status of the scan process.
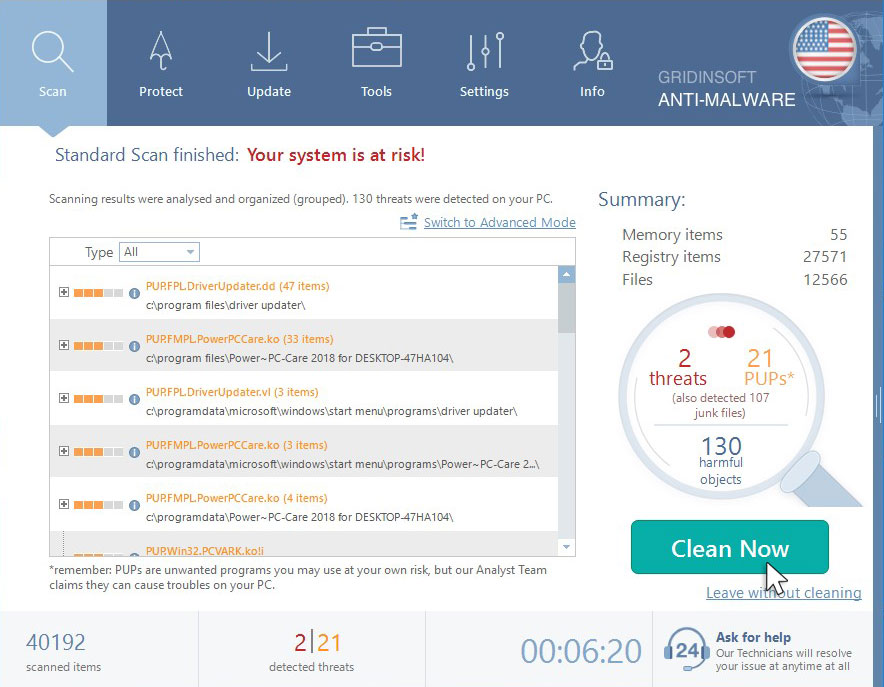
5. Click on “Clean Now”.
When the scan has completed, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.
Use Emsisoft Decryptor for restore foty files
You can get Emsisoft Decryptor by clicking the button below:
- Run the decryptor as an administrator. The license terms will show up, which you have to agree to by clicking the “Yes” button.
- Once the license terms are accepted, the primary decryptor user interface opens.
- By default, the decryptor will pre-populate the locations to decrypt with the currently connected drives and network drives. Additional locations can be added using the Add” button.
- Decryptors typically offer various options depending on the particular malware family. The available options are located in the Options tab and can be enabled or disabled there. You can find a detailed list of the available Options below.
- After you have added all the locations you want to decrypt to the list, click the “Decrypt” button to start the decryption process. The screen will switch to a status view, informing you about the current process and decryption status of your files
- The decryptor will inform you once the decryption process is finished. If you require the report for your personal records, you can save it by clicking the “Save log” button. You can also copy it straight to your clipboard to paste it into emails or forum posts if you are asked to.