Hacktivists Leaked Software and Documentation from Cellebrite and MSAB
The hacktivist group Enlace Hacktivista claims that an anonymous source gave it software and documentation from Cellebrite and MSAB, which provide law enforcement agencies around the world with tools to hack mobile devices and conduct other cyber-forensic operations.
Let me remind you that Cellebrite are independent cybercriminalists who specialize in extracting data from mobile devices (iOS and Android). For example, a few years ago, an Israeli firm was named the main candidate for the role of an FBI contractor when law enforcement officers were looking for specialists to hack the terrorist’s iPhone.In general, Cellebrite has repeatedly helped governments and law enforcement agencies of different countries to hack confiscated mobile phones (mainly by exploiting vulnerabilities ignored by device manufacturers), and has been criticized more than once by human rights activists and the media.
For example, we also wrote that Cellebrite says it can now hack the Signal messenger, and also that Cellebrite Company said that they are capable of unlocking any iOS-device and many devices on Android.
The forensic company MSAB from Sweden is also engaged in similar activities.
You might also be interested to know that US authorities can hack iPhone, but may have difficulties with Android.
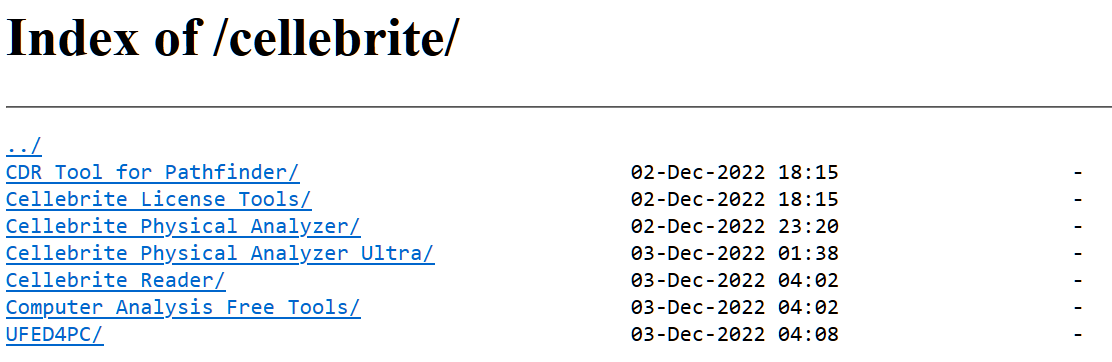
As representatives of Enlace Hacktivista now write, in their hands were 1.7 TB of Cellebrite data and 103 GB of MSAB data. The files have already been published in the public domain and are available for download through the DDoSecrets website, the Enlace Hacktivista website and via torrent.
Hacktivists recall that the tools of both companies are often used to collect information from the phones of journalists, activists and dissidents around the world, the companies themselves have been repeatedly accused of working with repressive regimes, and their software has been repeatedly used to directly violate human rights.



