38 Million User Records Leaked Due to Misconfiguration of Microsoft Power Apps
Security researchers from UpGuard have discovered more than 38 million public records belonging to 47 different organizations, apparently leaked to the network due to misconfiguration of Microsoft Power Apps.
PowerApps is a platform for business users. It allows creating custom business applications that run on mobile devices and the Internet, based on ready-made templates, and also offers APIs for providing access to data, including various options for obtaining and storing information.The leak reportedly affected government agencies in Indiana, Maryland and New York, as well as private companies, including giants such as American Airlines, Ford, JB Hunt and even Microsoft itself.
For example, 332,000 email addresses and employee IDs used to calculate payroll at Microsoft were publicly available, as well as more than 85,000 records associated with the Business Tools Support and Mixed Reality portals.
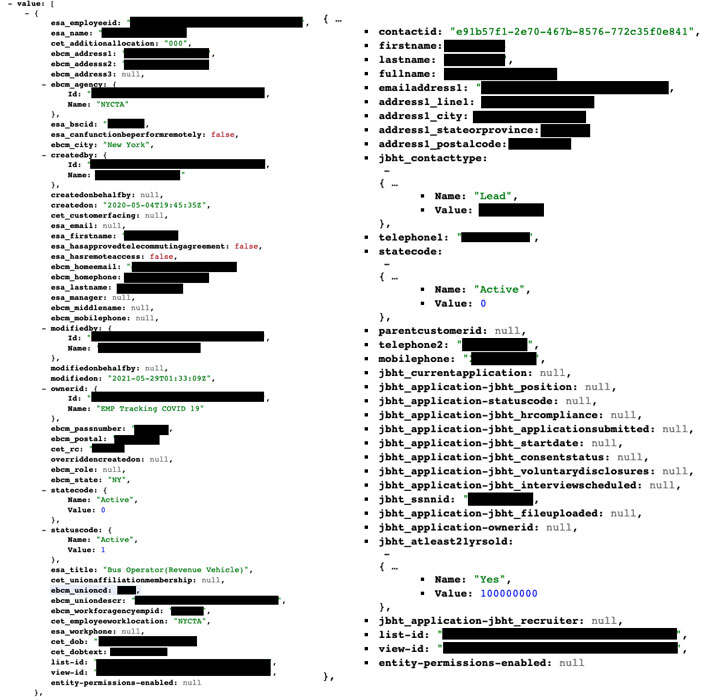
Experts write that all this data was available to anyone due to mistake and leaked through the OData PowerApps API. The problem lay in the misconfiguration of how exactly the portal can exchange data and store it. The fact is that to protect information, it is necessary not only to set specific Table Permissions for tables, but also to activate Enable Table Permissions. Alas, many did not.
Researchers notified Microsoft of the data breach as early as June 24, 2021, but at first the company refused to acknowledge this as a vulnerability and a problem, saying that this was a “deliberate” behavior of the system.
Let me remind you that we wrote that Microsoft and Eclypsium got into serious debate over Dell SupportAssist vulnerabilities.