Hackers stole the source codes of Puma’s applications
The hackers stole data (application source codes) from the Puma sportswear manufacturer applications and are now demanding a ransom from the company, threatening to publish the stolen information on the darknet.
The Record reports that the post with threats appeared on the Marketo website at the end of August. Robert-Jan Bartunek, head of Puma corporate communications, confirmed to reporters that the company suffered from the leak and said that some of the sources were in the hands of the hackers.
He also stressed that the incident did not affect user data.

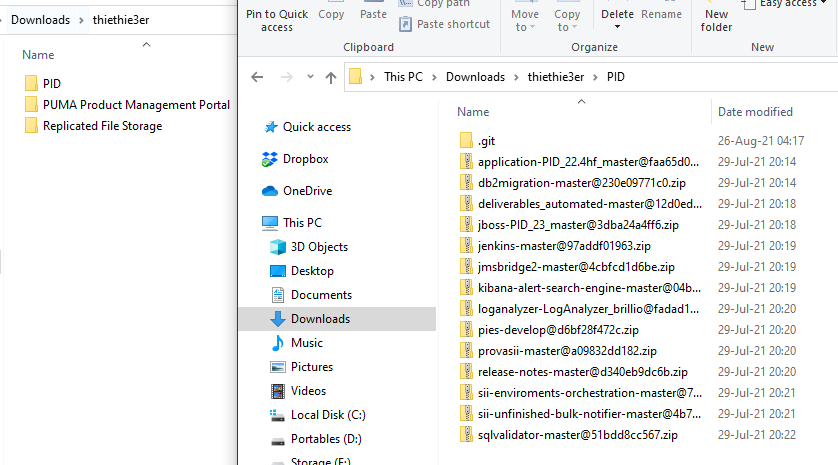
The hackers claim to have stolen more than 1 GB of data from the company. To back up these claims with evidence, the attackers released examples of some files that appear to have been taken from the official Puma Git repository.
The Marketo darknet resource has been operating since April 2021 by the following scheme: site operators make a list of future victims, and then add evidence of hacking them (usually a small archive). If the affected company refuses to pay, its data is either published on the site for free, or distributed only among the VIP-members of the resource.
The site claims to publish information provided by several hacker groups, but does not work with ransomware.
Let me remind you that we also talked about US brand and retailer Guess reported that customers’ personal data leaked following the ransomware attack in February.



