Fortinet research: cybercriminals work Monday to Friday and follow the trends
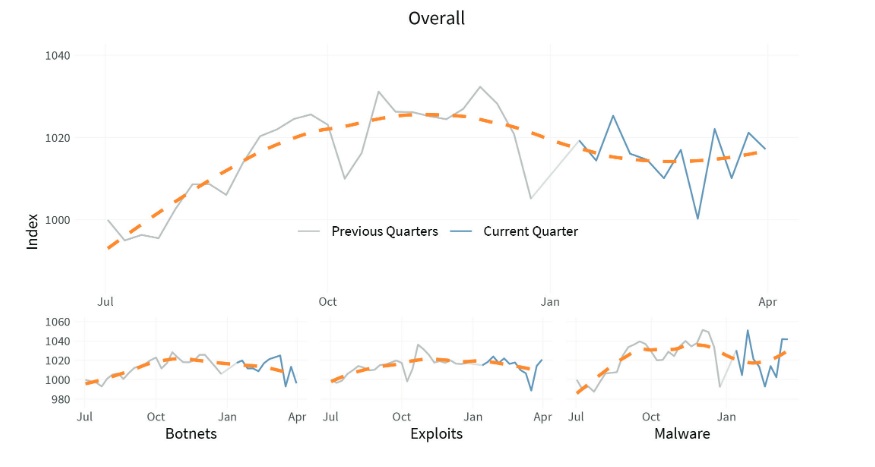
Fortinet published results of the newest quarterly report on global threats – Global Threat Landscape Report.
Research shows that cybercriminals improve methods of their attack, in particular, by using ransom programs, create personalized code for making a series of targeted attacks, and use LoTL-attacks and common infrastructure for expanding their opportunities.Research that aimed studying if attackers break their actions on several parts, and performing them in different days of the week, showed that cybercriminals are always trying to use opening opportunities maximally.
While comparing volumes of web-filtration in two phases of staged attacks (cyber kill chain phases) on weekdays and weekends, was discovered that activity prior to moment of compromising threefold higher during the weekdays, while traffic after compromising is less differentiated.
This is mostly explained by the fact that for seeking vulnerability is needed someone that would make certain actions, for example, follow the link in the fishing letter.
By contrast, there is no such necessity for active actions (command-and-control, C2), hence such activity can be noted any time. Cybercriminals realize it and try maximally use opportunities during the week, when users are more often online.
Read also: Fortinet research: last time considerably grew number of attacks on enterprise systems and networks
Usage of different web-filtration practices for weekdays and weekends plays important role for fuller understanding of different attacks’ kill-chains.
Extend of usage certain infrastructure by different threats allows concluding about important trends. Some threats more often than other use united infrastructure, while others need unique or specialized infrastructure.
About 60% of threats were done in the frames of one domains, and this indicates, that majority of bot-nets use already formed infrastructure.
Trojan IceID is an example of such approach “what is the need to buy or built if it can be taken for a while”. Moreover, when threats use some common infrastructure, they, as a rule, make it on the same kill-chain stage situations, when threat uses some domain for studying environment and finding vulnerabilities, and next in the same domain occurs C2 traffic transition, are quite seldom. This says that infrastructure plays special role in success of malware campaigns.
Understanding of threats that use same infrastructure and in what stages of kill-chain, enables organizations forecast potential points of development and changing of malware programs and bot-nets in future.
As a rule, attackers transit from one opportunity to other with the whole clusters, targeting most successful vulnerabilities and technologies that currently at the rise, to use opened opportunity instantly.
Example of new technology that cybercriminals pay attention to, are web-platforms that help users and enterprises in websites creation. These platforms, together with plugins from side developers, remain to be a common target for criminals.
This all confirms necessity of immediate installation of applications, and need from the side of organizations full understanding of the permanently developing world of cyberthreat, if they want to be a step behind hackers.
- Criminals’ activity before compromising is threefold higher during the weekdays while after compromising traffic is less differentiated.
- Some threats more often than other use united common infrastructure, than some special or unique infrastructures. Example of new technology that cybercriminals play special attention, are web-platforms that help users and enterprises in websites creation.
- Ransom programs did not disappear, but became more targeted on wealthy users.
- Attackers more and more often use double purpose tools or tools that are already installed on targeted systems and allow doing cyberattacks.
Source: https://www.fortinet.com



