In Croatia, the Police Arrested the Developer of NetWire RAT, and Authorities Sized the Malware Infrastructure
The international operation, in which the FBI and law enforcement agencies of many countries took part, led to the result that the police arrested the developer of the NetWire RAT malware and confiscated the domain with which the malware was distributed, as well as the hosting server.
Let me remind you that we also wrote that Police Arrested 55 Members of the Black Panthers for Stealing SIM Cards, and also that Student Who Ran One of the Largest Darknet Marketplaces in Germany Arrested.Also, the information security community reported that Ukrainian Law Enforcers Arrested Hackers Who Sold More Than 30 million Accounts.
NetWire was a remote access trojan and was sold on hacker forums and through the official website since 2012. The malware was advertised as a legitimate tool for remote administration and remote control of Windows-based computers. It was one of the cheapest and most used RAT Trojans.
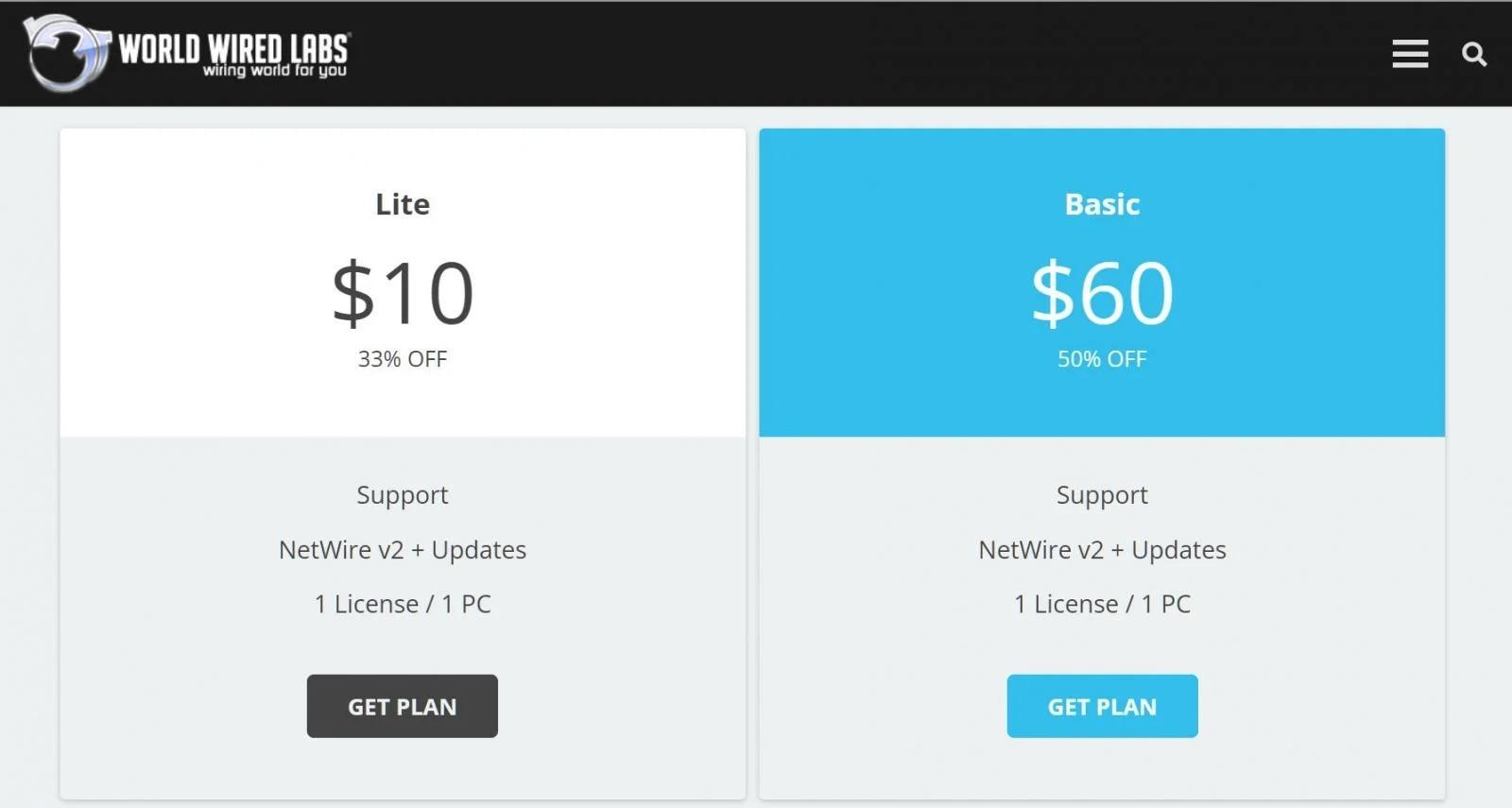
For example, at worldwiredlabs.com, users could subscribe for as little as $10 per month (support included).
Attackers could use the Netwire RAT to remotely take screenshots, download and upload files, execute commands, or download additional programs to run on infected computers.
The arrest warrant for the author of the Netwire RAT was issued on March 3, 2023, and last week, in a coordinated international operation, the developer was arrested in Croatia, according to the US Attorney’s Office for the Central District of California.
The FBI, the US Attorney’s Office, the Croatian Police, the Zurich Police, Europol, and the Australian Federal Police took part in the operation. So, law enforcement officers confiscated the already mentioned worldwiredlabs.com domain used to promote malware, and the Swiss police seized the server hosting the site. Now the site displays a special “stub” that reports the confiscation (see the illustration above).

Although law enforcement officers have not released the name of the suspect, well-known cybersecurity journalist Brian Krebs conducted his own investigation.
The WorldWiredLabs website first went online in February 2012 using a dedicated host with no other domains. The site’s real WHOIS registration records have always been hidden by privacy protection services, but there are plenty of clues in the historical Domain Name System (DNS) records for WorldWiredLabs that point in the same direction.
In October 2012, the WorldWiredLabs domain moved to another dedicated server at 198.91.90.7, which hosted another domain: printschoolmedia[.]org, also registered in 2012.



