Ransomware increasingly destroying user data by mistake
Coveware specialists summed up the results of the fourth quarter of 2020 and reported that they received many reports that ransomware is increasingly destroying entire clusters of services and data.
So, ransomware usually targets backup systems and machines of important targets, but in the cases mentioned there was nothing to recover.Experts say that financially profitable hackers are not doing this on purpose, because after the data is deleted, victims no longer have a reason to pay the hackers a ransom and thus “buy” the decryptor.
“The uptick in haphazard data destruction has led some victims to suffer significant data loss and extended business interruption as they struggle to rebuild systems from scratch. It remains unclear whether these events have been outliers or a symptom of less experienced bad actors handling the attack execution”, — Coveware researchers said.
Analysts believe that these incidents could be a consequence of the fact that the scene has recently been flooded with less skilled attackers. Even worse, this trend could continue into 2021.
Let me remind you about the case, when due to the hackers’ mistake, the stolen data became available through Google.
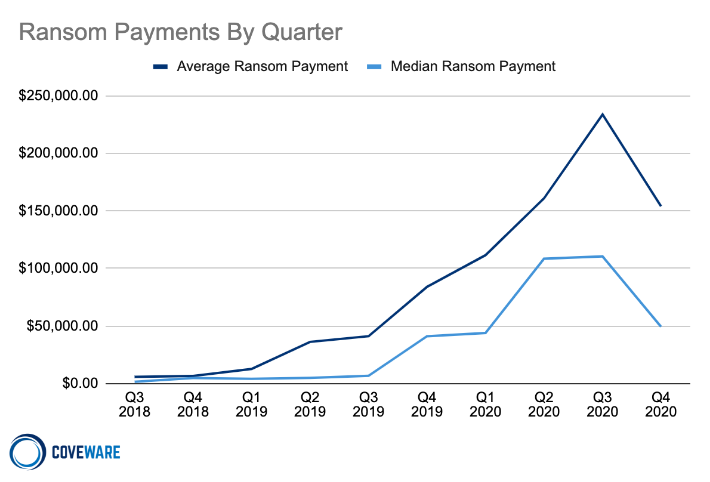
Coveware statistics also show that the average size of the paid ransom in the fourth quarter of 2020 decreased immediately by 34% ($154,108 versus $233,817). If you look at the median value, the drop will be even more significant: from 110,532 to 49,450 dollars, that is, by 55%.
The company’s report states that more and more often affected companies say :enough is enough” and prefer not to pay cybercriminals, despite the threats of the latter to “leak” the stolen data into the public domain.
The fact is that in 50-70% of cases, attackers claim that before encrypting the files, they managed to steal information from the victim company. However, this is often a lie, or hackers publish stolen data, regardless of whether they were paid or not. As a result, this pressure lever seems to be working less and less.
“With more companies falling victim, more are having the opportunity to constructively consider the trade offs, and are increasingly choosing not to pay. Attacking the raw economics of the cyber extortion economy from multiple angles is the best way to retract the volume of attacks. When fewer companies pay, regardless of the reason, it causes a long term impact, that compounded over time can make a material difference in the volume of attacks”, — explained Coveware specialists.
We also wrote that the security provider Emsisoft, in collaboration with Coveware, announced that they would provide a completely free ransomware recovery service for critical hospitals and other healthcare providers.



