Let’s Encrypt developers solved the problem of old Android devices
In the fall, Let’s Encrypt developers warned that in 2021, users of devices running Android 7.1 (Nougat) and older versions of the OS may experience serious problems with certificates and access to sites.
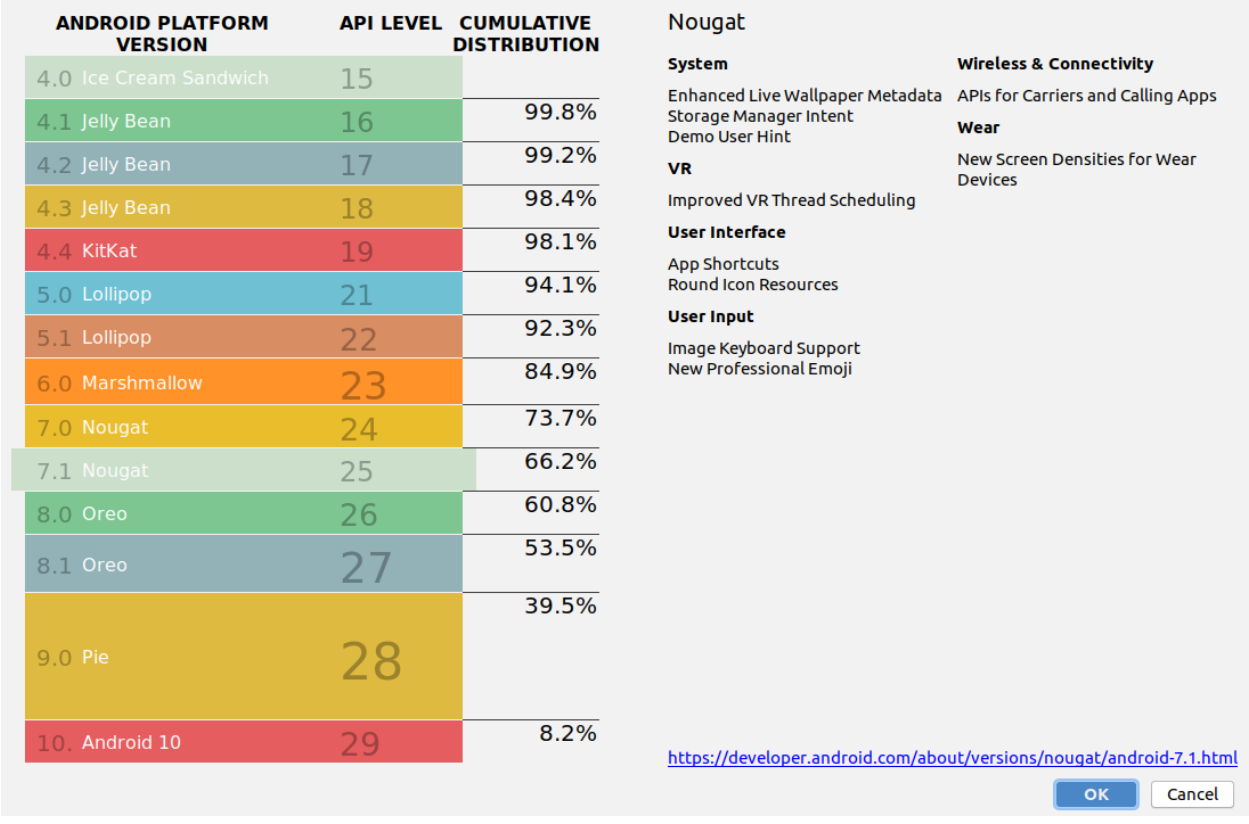
Unfortunately, there are still about 34% of such old devices in the Android ecosystem.Let me remind you that the problem is that on September 1, 2021, the partnership between Let’s Encrypt and the IdenTrust organization expires, and companies have no plans to extend it. This means that a Let’s Encrypt root certificate that is cross-signed with IdenTrust DST Root X3 will also expire on September 1, 2021.
“This will not cause any problems on most modern operating systems, as Let’s Encrypt has its own ISRG Root X1 certificate for a long time, and most operating systems and browsers can work with it. However, this does not apply to older versions of Android that have not been updated since 2016. They don’t trust their own Let’s Encrypt root certificate, and this is likely to cause problems with these devices”, – said representatives of Let’s Encrypt.
As a result, it was assumed that in the fall of 2021, users of older devices will begin to experience difficulties in accessing sites and will receive messages about certificate errors. Let’s Encrypt engineers estimate that these users account for about 1-5% of all traffic.
By the way, in March, Let’s Encrypt revokes 3 million certificates due to a bug.
Let’s Encrypt said yesterday that they have found a solution to the problem that will allow older Android devices to continue working. Essentially, the solution is to just keep using the expired certificate from IdenTrust.
“IdenTrust has agreed to issue a three-year cross-signature for our ISRG Root X1 from their DST Root CA X3. This will work a bit innovatively, as the signature will continue to be valid after the DST Root CA X3 expires. This solution works because Android does not intentionally enforce expiration dates for certificates used as trust anchors”, – said in Let’s Encrypt.
The self-signed certificate represented by the CA X3 DST Root key pair is about to expire. However, browser and OS root stores do not contain certificates per se, they contain so-called “trust anchors” and standards for validation that allow implementations to choose whether to use these trust anchors.
Android intentionally chose not to use the notAfter field for trust anchors. Since ISRG Root X1 was not added to the old Android Trusted Stores, the DST Root CA X3 was not removed.
Thus, it can issue a cross-signature that is valid longer than the self-signed certificate itself.
The new cross-signature will expire in early 2024, and by that time, number of Android devices with operating systems released in 2016 and earlier should be marginal.
Let me remind you that Patches for Android now come to users faster.



