Hacker broke into T-Mobile via vulnerable router
21-year-old hacker John Binns, who lives in Turkey and is possibly a member of ISIS, claims to broke into T-Mobile through a vulnerable router. The head of the T-Mobile company also shared data on how the attack was carried out.
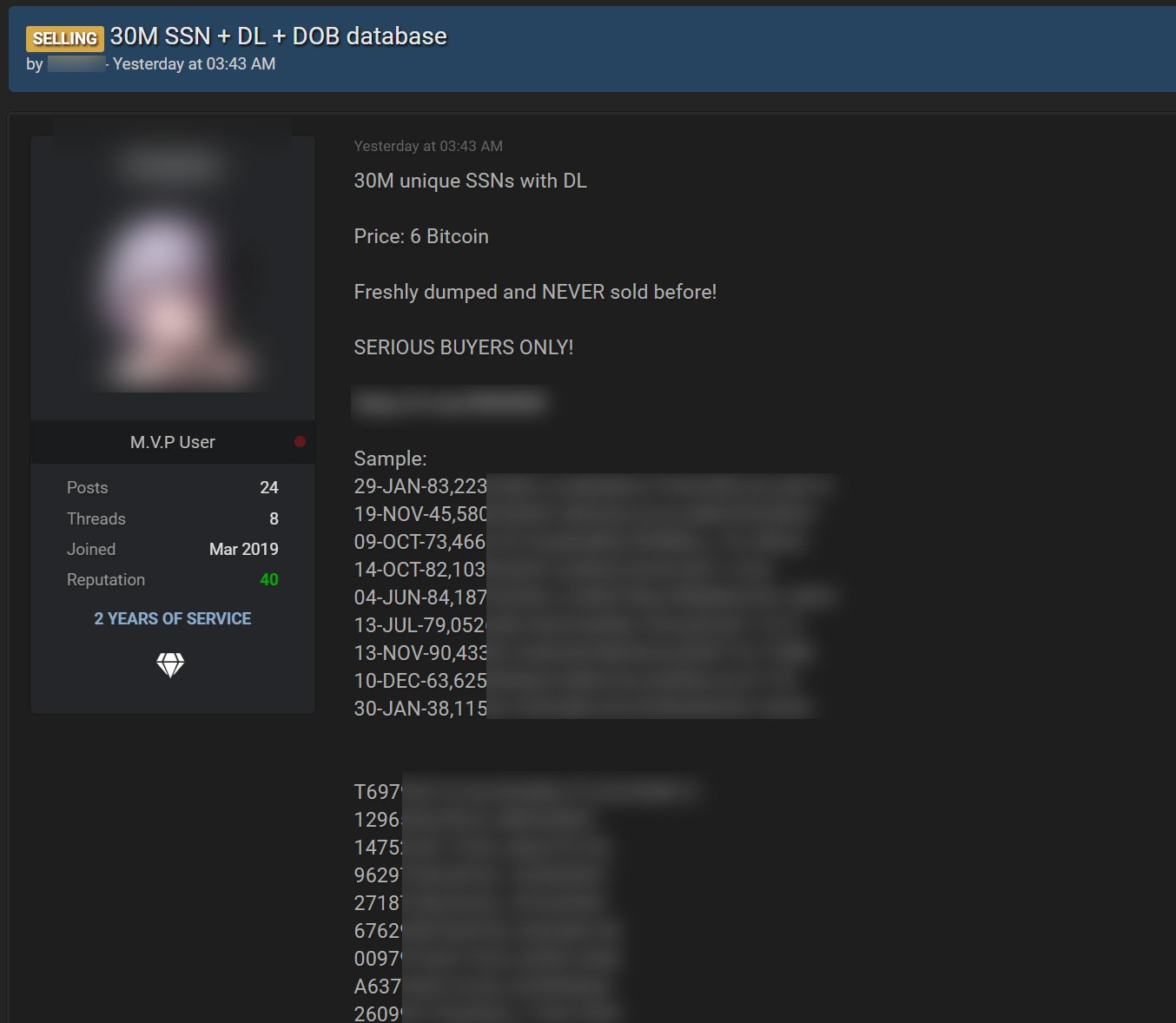
Let me remind you that a large-scale data leak became known in mid-August, when an announcement appeared on a hacker forum about the sale of personal data of approximately 100 million T-Mobile customers. The seller claimed that two weeks ago, he hacked into the company’s servers (production, staging, and development servers, including the Oracle server containing customer data), gaining access to an unsecured T-Mobile GPRS gateway, and stole the data from there.Hacker estimated the entire dump at 6 bitcoins (about $280,000), claiming that in total the database contains information on 100 million people, including IMSI, IMEI, phone numbers, names, security PINs. Worse, some 30 million more people were given birth dates, driver’s license numbers, and even social security numbers.
Soon, representatives of T-Mobile confirmed that the hack did take place, but the company did not provide any details of what happened at the time. A little later, the company reported that the incident really affected millions of users: in total, records belonging to 50 million people were stolen, including current, former or potential customers of T-Mobile.
In a statement released late last week, CEO Mike Sievert said that while the investigation into the incident is almost complete, he is unable to share in-depth technical details of the incident due to a criminal investigation currently underway by law enforcement. However, Sievert did reveal some details.

Shortly before this statement of the company, the journalists of The Wall Street Journal reported that they managed to get in touch with the hacker who attacked T-Mobile. The responsibility for the attack took 21-year-old John Binns, a US citizen now residing in Turkey.
In an interview that Binns gave via Telegram, he claimed to have hacked company out of revenge and a desire to draw attention to the problem. The fact is that last year he filed a lawsuit against the CIA, FBI and other US government agencies, claiming that he was blackmailed, followed and tortured. Binns claims that the US government suspects him of running the Satori botnet, and also suspects that he is a member of ISIS (Binns denies both charges).
In an interview with The Wall Street Journal reporters, Binns recounted everything that he had previously stated in his lawsuit, and also said that US law enforcement agencies had previously abducted him in Germany and Turkey, and had also been placed in a psychiatric hospital against his will. In response, the hacker decided to “damage US infrastructure.”
Binns also said that he managed to hack T-Mobile through a misconfigured router, which he discovered back in July. He says he found the router using a simple, publicly available tool, and some are suggesting that it is Shodan, Nmap, or Masscan.
Allegedly, this router provided Binns with an entry point to T-Mobile servers located in the data center in Washington state, and from where he was able to develop the attack further, having obtained credentials that gave him access to more than 100 of the company’s servers. Binns described T-Mobile’s security as “appalling,” and said it took him about a week to get to the servers storing customer data and hack it.



