Cyber espionage group Cloud Atlas added to its arsenal new polymorphic malware
Kaspersky Lab researchers said that the Cloud Atlas group (also known as Inception), whose activities experts have monitored since 2014, has expanded its arsenal and is now using a new polymorphic malware.
Cloud Atlas is primarily focused on cyber espionage operations, with hackers targeting industry and governmental organizations. Since beginning of 2019, group’s fishing campaigns have been mainly focused on Russia, Central Asia, Turkey and some regions of Ukraine.
Analysts say that in general, since 2018, the group has been relying on tactics and malware that have already proven their effectiveness.
So, hackers still use fishing emails to identify large victims. Such emails are completed with Office documents that use malicious remote templates hosted on remote servers. Experts from Palo Alto Networks have already described this tactic of the grouping.
Read also: Google Play clicker Trojan installed over 100 million times
Earlier, immediately after exploiting the vulnerabilities CVE-2017-11882 (in Microsoft Equation) and CVE-2018-0802, hackers exploited their PowerShower malware.
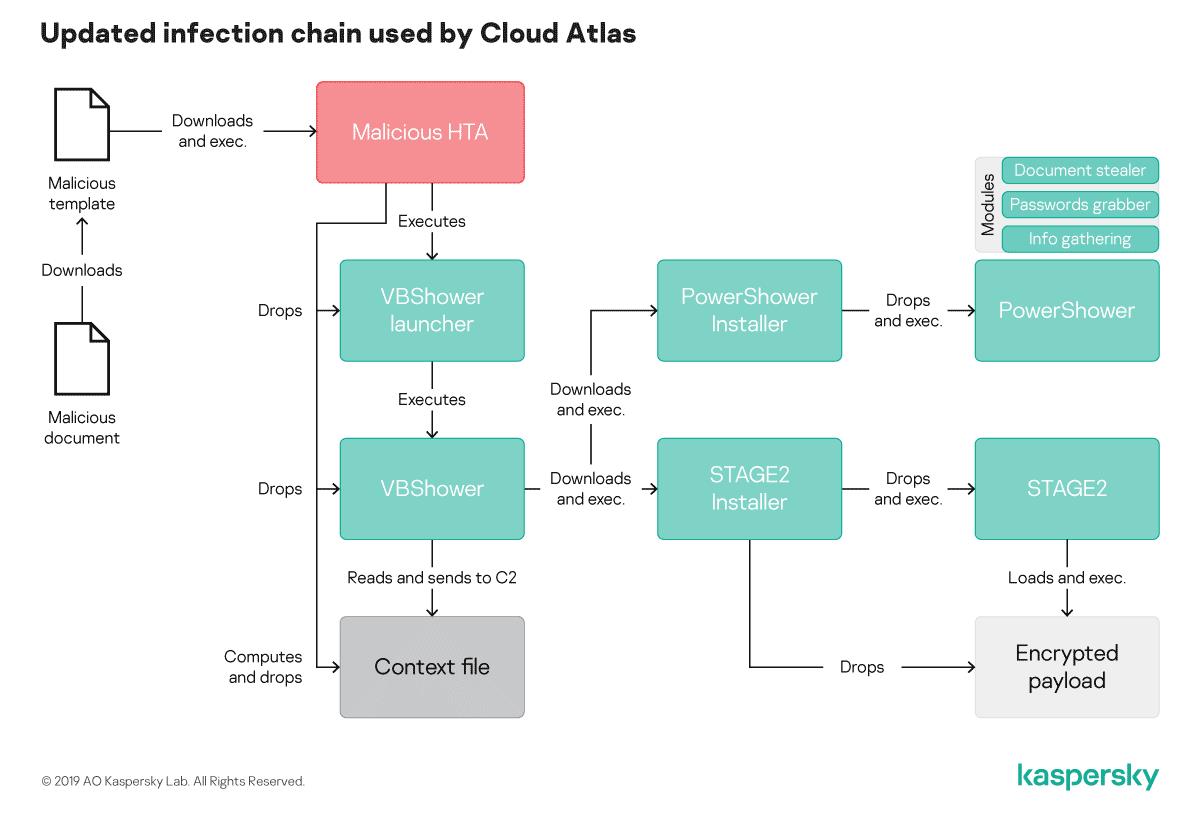
However, in recent months, the chain of infection has changed. Now it also includes polymorphic HTA (HTML application – approx. VK), a new polymorphic VBS implant, VBShower, designed to perform PowerShower and a modular backdoor of the second stage of infection, which was described by researchers five years ago and has not changed since then.
“This “polymorphic” infection chain allows the attacker to prevent IoC-based defence, as each code is unique so vicrim can’t be searched via file hash on the host”, — say researchers.
In addition, before using the second stage bootloader, VBShower will also ensure that all evidence about presence of the malware is removed from the system. So, it tries to delete all files contained in% APPDATA% \ .. \ Local \ Temporary Internet Files \ Content.Word and% APPDATA% \ .. \ Local Settings \ Temporary Internet Files \ Content.Word \
As a result, a new, more complicated infection chain is as follows: