Rise of the Machines is coming: bots pretend to be humans with the new trick
As report Akamai company specialists, malware programs operators armored with the new technique of bypass detection.
Method is called “Cipher Stunting» and allows pretending that generated by bots traffic is generated by real people.Technique is in changing sent by bots ClientHello messages.
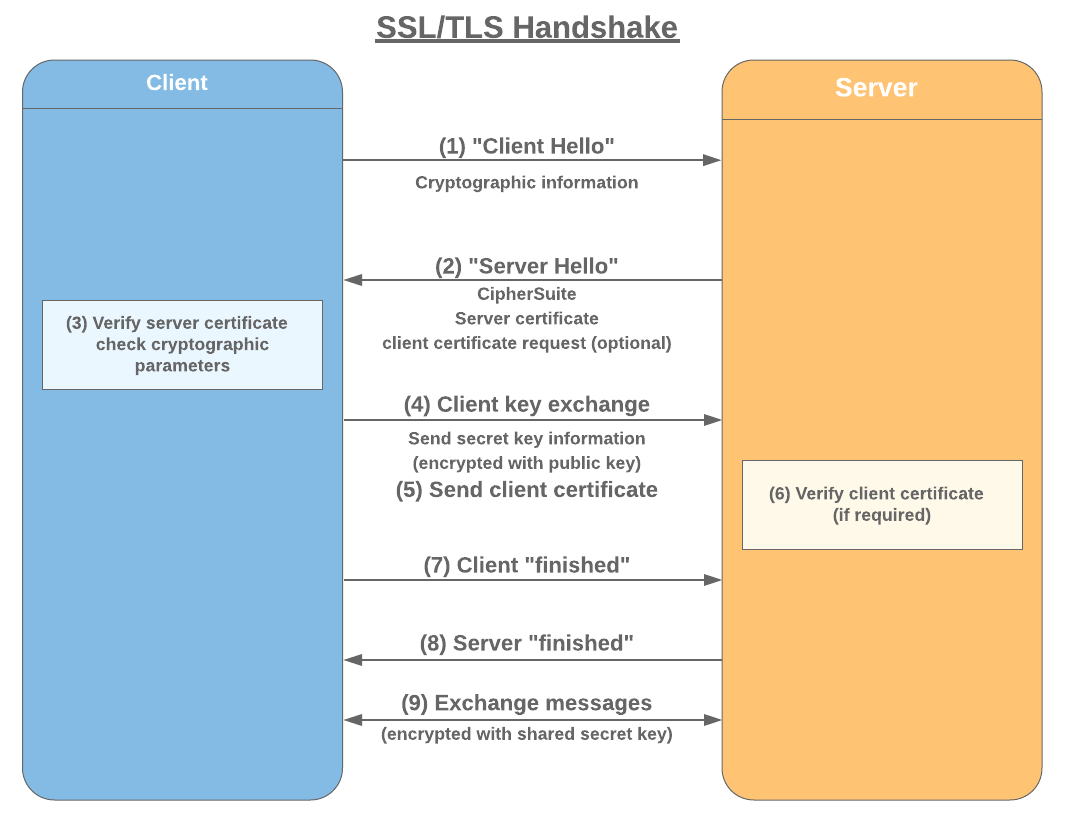
ClientHello is a first packet with data about communication parameters (of necessary TLS version, applied encryption methods and supported compression methods), transited to server in the process of handshake. These data is not encrypted, due to it security mechanisms can analyze client’s fingerprints and differentiate legitimate and malware traffic.
With the help of “Cipher Stunting” attackers can cheat tools for taking digital fingerprints and present malware traffic as a legitimate one.
As Akamai specialists explained, most often website data transition is performed by HTTPS (HTTP over SSL/TLS) protocol. Data about the client server gets during TLS-handshake, and with its help differs legitimate and malware traffic. Nevertheless, attackers learned to modify signatures and cheat websites security mechanisms.
“A majority (~82%) of the malicious traffic (including application attacks, web scraping, credential abuse, etc.) Akamai witnesses is carried out using secure connections over SSL/TLS. This number has grown over the last few years”, — told Moshe Zioni, Director of Threat Research of Akamai.
As a rule, cybercriminals bypass security mechanisms by randomization of SSL/TLS signature. However, “Cipher Stunting” significantly differs from such approach, as for changing of TLS-fingerprint encryption itself randomized.
According to Akamai data, by the end of February 2019 was noted 1,3 billions of TLS-signature modification that is 20% more than in October 2018.
Source: https://blogs.akamai.com